Most manufacturing business owners think of cybersecurity as a problem for the office, something that protects email accounts and accounting software. That assumption is costly. A single successful cyberattack on a manufacturing operation can freeze production lines, corrupt machine programming, leak proprietary designs, and trigger regulatory penalties that take months to resolve. Small manufacturers are increasingly targeted because attackers know they often carry valuable contracts and data but operate with leaner IT resources than large enterprises. This guide explains what actually works, what regulators expect, and how to move forward without overwhelming your team.
Table of Contents
- Why cybersecurity matters for manufacturing operations
- Core methodologies for defending manufacturing systems
- Regulatory pressures: CMMC, NIST, and industry compliance
- Starting points for SMBs: Free resources and practical steps
- A fresh perspective: What most manufacturing guides miss
- Protect your manufacturing operation with expert support
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| OT security is critical | Operational technology on the factory floor faces unique threats and must be protected alongside IT systems. |
| Start with basics | Simple steps like multi-factor authentication, network segmentation, and regular backups deliver strong initial security for SMBs. |
| Regulations require preparation | CMMC 2.0 compliance takes months and demands thorough documentation and third-party assessment. |
| Use free resources | NIST CSF Quick Start and CISA CPGs provide practical, cost-effective tools to build foundational cybersecurity. |
| Phased approach wins | Prioritizing key controls and gradual implementation beats an all-at-once strategy for small manufacturers. |
Why cybersecurity matters for manufacturing operations
To ground the topic, let's examine exactly why manufacturing is so exposed and what can go wrong if cybersecurity is ignored.
Manufacturing operations run on two distinct technology environments that both need protection. IT (Information Technology) covers the systems most people recognize: computers, servers, email, ERP software, and business networks. OT (Operational Technology) refers to the hardware and software that directly controls physical processes on the production floor: programmable logic controllers (PLCs), sensors, SCADA systems, and industrial control systems (ICS). These two worlds used to be separate. Increasingly, they are connected, and that convergence opens serious new risks.
When OT systems connect to business networks or the internet, attackers can pivot from a compromised office laptop straight into the production environment. That's what cybersecurity professionals call lateral movement, and it's particularly dangerous in manufacturing because legacy ICS/OT vulnerabilities, including the absence of basic encryption and user authentication, make it straightforward for an attacker to move across systems undetected.
"OT cybersecurity is often under-resourced in manufacturing environments, leaving critical production systems exposed even when office IT is relatively well protected." — CISA Cross-Sector Cybersecurity Performance Goals
The consequences are not abstract. When ransomware hits a manufacturing network, production stops. Orders go unfulfilled. Customers find alternative suppliers. According to SANS Institute data cited in CISA's guidance, 40% of OT incidents result in measurable operational disruption. That means lost revenue, overtime costs to catch up on backlogged orders, and potential contractual penalties with customers.
Beyond the operational impact, there are compliance consequences. Defense contractors face CMMC requirements. Medical device manufacturers must align with FDA regulations. Food producers deal with FDA and USDA rules. A breach that exposes Controlled Unclassified Information (CUI) can cost a company its government contract entirely.
Common threats small manufacturers face include:
- Ransomware attacks that encrypt both IT and OT data, halting production until a ransom is paid or systems are restored from backup
- Remote access exploitation through poorly secured VPNs or remote desktop protocols used by vendors and technicians
- Phishing campaigns targeting employees with access to financial systems or engineering files
- Supply chain attacks that introduce malicious code through trusted software vendors
Our manufacturing network security guide covers these attack vectors in greater detail, but the core message is clear: protection must cover both your office and your floor.
Core methodologies for defending manufacturing systems
Given these risks, what practical tactics can small manufacturers deploy to defend their operations?

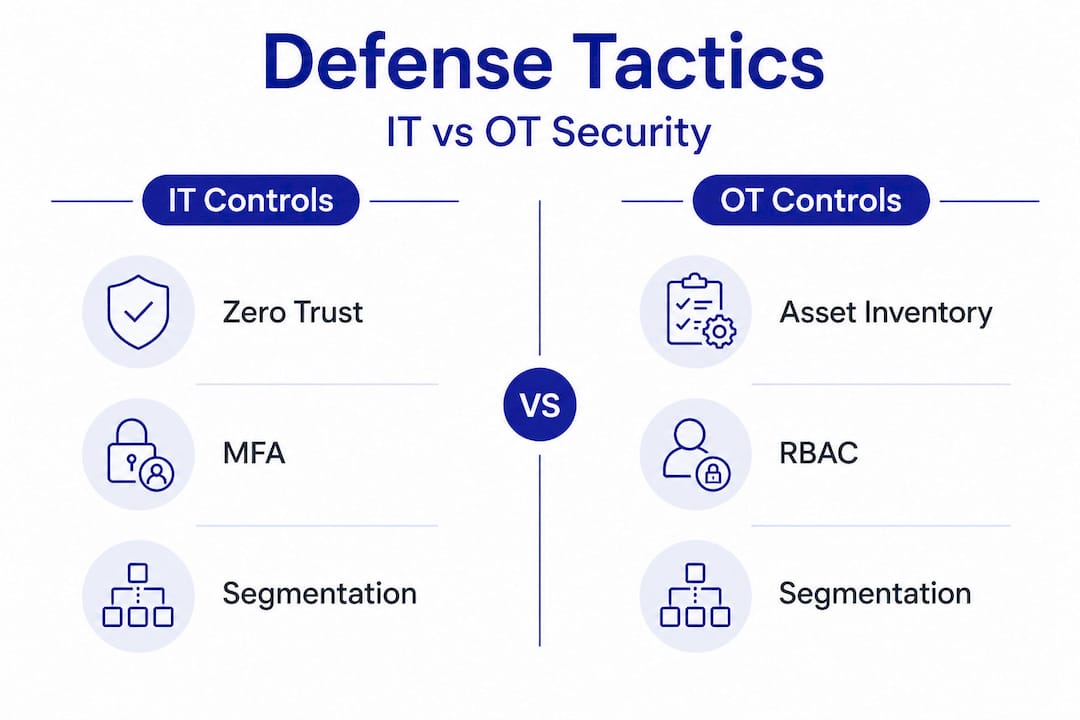
Several proven methodologies form the backbone of a solid manufacturing cybersecurity program. Understanding each one helps you prioritize investments and communicate needs to your IT team or managed service provider. According to CISA's ICS security guidance, the following controls are foundational for protecting both IT and OT environments.
Zero Trust means no user, device, or system is automatically trusted, even if it's already inside the network. Every access request gets verified continuously based on identity, device health, and context. This is especially relevant in manufacturing where contractors, vendors, and remote technicians frequently access systems.
Network segmentation separates IT and OT networks so that a breach in one zone can't automatically spread to the other. Microsegmentation takes this further by creating smaller isolated zones within each network. Think of it as firebreaks: even if one section catches fire, the rest of the operation stays intact.
Multi-factor authentication (MFA) requires users to verify identity with at least two factors, such as a password plus a mobile app code. It's one of the most effective controls available and prevents the vast majority of credential-based attacks.
Role-based access control (RBAC) ensures employees can only access the data and systems their job actually requires. A machine operator doesn't need access to financial records. A billing clerk doesn't need access to production control software.
Asset inventory means knowing every device on your network, including OT equipment that rarely changes but is often overlooked. You can't protect what you don't know you have.
| Control | IT application | OT application |
|---|---|---|
| Zero Trust | Verify users before granting app/data access | Validate technician and vendor access to control systems |
| Network segmentation | Separate finance, HR, and engineering networks | Isolate PLCs and SCADA from business LAN |
| MFA | Office 365, VPN, remote desktop logins | Remote access to industrial systems |
| RBAC | Restrict file server and database access | Limit who can modify machine programming |
| Asset inventory | Catalog servers, workstations, and laptops | Document sensors, PLCs, HMIs, and control panels |
Phased implementation is realistic and necessary, particularly when legacy OT equipment is involved. Older PLCs often can't support modern authentication protocols, so you work around them with segmentation and monitoring rather than trying to upgrade everything at once. Review segmentation best practices to understand how to architect your network in stages that minimize production risk.
Start with your directory environment too. Hardening Active Directory, which is the service that manages user logins across Windows systems, closes many common attack paths. Our directory hardening guide walks through practical steps. Similarly, if your team uses Microsoft 365, applying the right security configurations matters enormously, and our Microsoft 365 security tips cover the essentials.
Pro Tip: Before investing in advanced security tools, make sure MFA is turned on for all remote access and cloud accounts, segment your OT network from your business network, and verify that your backup system actually works by testing a restore. These three steps stop the majority of successful attacks on small manufacturers.
Regulatory pressures: CMMC, NIST, and industry compliance
With hands-on security covered, regulatory compliance is the next hurdle. Here's what small manufacturers must know about rules, timelines, and hidden traps.
The regulatory landscape for manufacturing has grown significantly more demanding. Two frameworks dominate for most small U.S. manufacturers, especially those doing business with the Department of Defense or federal agencies.
| Framework | Who it applies to | Key requirement | Assessment type |
|---|---|---|---|
| CMMC 2.0 Level 2 | Defense contractors handling CUI | 110 NIST 800-171 controls | Third-party assessment (C3PAO) |
| NIST SP 800-171 | Federal contractors and subcontractors | 110 security requirements across 14 domains | Self-assessment or third-party |
| NIST Cybersecurity Framework (CSF) | Any organization, voluntary | Identify, Protect, Detect, Respond, Recover | Self-assessment |
| FDA 21 CFR Part 11 | Medical device and pharma manufacturers | Electronic records and signature controls | Regulatory audit |
CMMC 2.0 Level 2 requires all 110 controls from NIST 800-171, verified by a certified third-party assessment organization (C3PAO). Many small manufacturers are simply unprepared for what that means in practice. The assessment evaluates not just whether controls are in place but whether they are documented, consistently applied, and supported by evidence.
Common compliance mistakes that delay timelines for small manufacturers include:
- Underestimating scope. Companies assume CMMC only applies to a handful of systems, then discover that CUI flows through many more systems, applications, and processes than expected.
- Starting documentation late. Assessors need policies, procedures, and logs. Creating that documentation from scratch during the assessment period adds months.
- Ignoring subcontractors. If you pass CUI to a supplier or subcontractor, they may also need to comply, and their readiness becomes your problem.
- Treating compliance as a one-time project. CMMC requires continuous compliance, not just a passing score at a single point in time.
NIST guidance for small businesses recommends using the NIST CSF Quick Start as a starting point and outsourcing when internal resources are limited. Importantly, that same guidance notes that CMMC preparation typically takes 6 to 12 months, a timeline many small manufacturers discover far too late.
Pro Tip: Scope your CUI enclave carefully. A CUI enclave is the defined boundary of systems that actually store, process, or transmit Controlled Unclassified Information. The smaller and tighter that boundary, the fewer systems fall under CMMC scope, which reduces assessment cost and speeds up the process significantly. Work with a compliance advisor to define this boundary before you start technical implementation.
Our CMMC requirements guide provides a detailed breakdown of each level's obligations. If your operation also touches FDA requirements, our 21 CFR compliance tips address electronic record controls relevant to manufacturers in regulated industries.
Starting points for SMBs: Free resources and practical steps
Whether you're facing a long compliance process or just starting, here's how you can make progress today, often for free.
The good news is that the federal government has invested heavily in producing free, practical cybersecurity resources tailored to organizations with limited budgets and staff. Most small manufacturers simply aren't aware these tools exist.
The two most valuable free resources right now are:
- NIST CSF Quick Start Guide: A streamlined version of the full NIST Cybersecurity Framework designed specifically for small businesses. It walks through five core functions (Identify, Protect, Detect, Respond, Recover) with practical worksheets and prioritized action steps.
- CISA Cross-Sector Cybersecurity Performance Goals (CPGs): A baseline set of controls CISA recommends for all critical infrastructure sectors, including manufacturing. These are written clearly and focused on the most impactful protections.
NIST's small business cyber guidance explicitly recommends outsourcing cybersecurity functions if your organization lacks internal capacity, and notes that CMMC preparation takes 6 to 12 months even with outside help. Starting now is always better than starting after an incident.
Here are practical first steps any small manufacturer can take immediately:
- Run an asset inventory. List every device connected to your network, including machines on the floor.
- Enable MFA on all remote access and cloud accounts. This is free in most cases and takes hours, not weeks, to implement.
- Separate your OT and IT networks. Even a basic VLAN (virtual local area network) configuration provides meaningful protection.
- Test your backups. Know that you can actually restore critical data if ransomware hits.
- Conduct a gap analysis against NIST 800-171. Use the NIST self-assessment guide to score your current state honestly.
Pro Tip: Outsourcing doesn't mean losing control. A managed IT partner can handle the monitoring, patching, documentation, and compliance groundwork while your team stays focused on production. The cost is nearly always lower than hiring even a single in-house IT security analyst.
Our practical cyber guide provides a step-by-step walkthrough for small manufacturers starting from scratch.
A fresh perspective: What most manufacturing guides miss
Most cybersecurity guides written for manufacturers read like checklists: enable MFA, segment networks, train employees, repeat. That advice is correct. But following it all at once without a clear priority order is where small manufacturers get stuck, and sometimes get hurt.
The real problem isn't lack of knowledge. It's that manufacturers try to implement everything simultaneously across both IT and OT, then stall when they hit legacy equipment that can't support modern controls. Progress stops. The project gets shelved. And the business remains exposed.
What actually works is a staged approach built around risk. Identify your most critical systems first, those that if compromised would stop production or violate a contract. Protect those first with segmentation, MFA, and tested backups. Then expand the perimeter outward in phases, addressing legacy OT equipment through compensating controls (like monitoring and segmentation) rather than waiting for a full hardware refresh that may never happen.
The second thing most guides miss is the CUI scoping issue. Small manufacturers frequently underestimate CMMC scope, discovering mid-assessment that far more systems touch CUI than they realized. That error alone causes 6-plus month delays and significant unplanned cost. Getting scoping right before you start technical work is arguably the highest-value activity a defense contractor can do.
Third, and perhaps most overlooked, is that free government resources go almost completely unused. NIST, CISA, and the Department of Defense have produced practical, actionable tools at no cost. Small manufacturers who engage with these resources and apply them systematically gain both better security and better audit readiness. For a deeper look at why investing in managed cybersecurity services pays off even at the SMB level, see our article on essential cyber protection.
The bottom line is that progress beats perfection. A phased, risk-prioritized approach executed consistently will always outperform a comprehensive plan that never moves past the planning stage.
Protect your manufacturing operation with expert support
Symmetry Network Management works with small U.S. manufacturers to build practical, compliant cybersecurity programs without the overhead of a full internal IT department. Whether you're starting from zero or preparing for a CMMC assessment, our team brings the expertise and hands-on support to move you forward.

Our managed IT and cybersecurity services include 24/7 system monitoring, endpoint security, firewall management, backup and recovery, and direct compliance assistance for frameworks like CMMC and NIST 800-171. We use fixed pricing so there are no surprise invoices, and our support team is U.S.-based for fast, knowledgeable responses. If you want to understand exactly where your gaps are, we offer a free security assessment to identify your most pressing risks and give you a clear starting point. Talk to our team today and put a practical plan in place before the next incident makes it urgent.
Frequently asked questions
What's the difference between IT and OT cybersecurity in manufacturing?
IT cybersecurity focuses on protecting office computers, business data, and enterprise software, while OT cybersecurity secures the production floor equipment including sensors, PLCs, and control networks that run physical processes. Both require protection because OT is often under-resourced and increasingly connected to business IT systems.
How long does CMMC 2.0 compliance typically take for small manufacturers?
CMMC preparation takes 6 to 12 months for most small manufacturers, with delays most commonly caused by documentation gaps and underestimating the scope of systems that handle CUI.
What are affordable ways for a small manufacturer to start improving cybersecurity?
Begin with free tools like the NIST CSF Quick Start, enable MFA across all remote access accounts, segment your OT and IT networks, and test your backup and recovery process. Outsourcing to a managed cybersecurity provider is also a cost-effective option for small teams.
Why are legacy OT systems so vulnerable?
Legacy ICS and OT systems were designed for reliability, not security. They typically lack encryption and user authentication, which makes it easy for attackers to move laterally through manufacturing networks once they gain an initial foothold.
Recommended
- How to Secure Manufacturing Networks: A Practical SMB Guide | Symmetry Network Management
- Why use cybersecurity services: Essential protection for SMBs
- 21 CFR Part 11 Cybersecurity Compliance Guide | Symmetry Network Management
- 5 Critical Security Controls Every Small Business Needs | Symmetry Network Management
- Technical Email Nurturing for Manufacturers
