A firewall sitting quietly in your server closet is not the same as a firewall actively protecting your business. Many small business owners assume that having one installed is enough, but that assumption leaves real gaps in your security posture. Firewalls serve as the primary barrier between your trusted internal network and the untrusted outside world, monitoring and controlling traffic based on defined security rules to block unauthorized access, malware, and other threats. This guide walks through how firewalls work, which types fit different business environments, and how to use them as part of a layered defense strategy that actually holds up.
Table of Contents
- What is a firewall and why does it matter?
- Types of firewalls: Choosing the right protection for your business
- How firewalls protect small businesses: Core functions and layered defense
- Manufacturing, OT, and the special demands of industrial firewalls
- Nuances, pitfalls, and best practices in firewall management
- Why the conventional wisdom about firewalls is incomplete
- How Symmetry Network Management helps you maximize firewall protection
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Primary security barrier | Firewalls serve as the first line of defense against unauthorized access and threats for small businesses. |
| Choosing the right type | Selecting NGFW or stateful firewalls depends on your business's complexity and specific needs. |
| Layered defense is critical | Pairing firewalls with antivirus and active management provides much stronger protection. |
| Avoid common pitfalls | Proper rule management and pre-deployment simulations help prevent risky misconfigurations. |
| Industry needs matter | Specialized firewalls and network segmentation are essential for manufacturing and industrial networks. |
What is a firewall and why does it matter?
A firewall is a security system, either hardware, software, or a combination of both, that inspects network traffic and decides what to allow or block based on a set of rules. Think of it as a security checkpoint at every entry point to your building. Nothing gets in or out without being checked against an approved list.
The core job of a firewall is to enforce boundaries. It separates your internal systems from the outside internet, controls which applications can communicate over your network, and blocks traffic that matches known threat patterns. That sounds straightforward, but the execution matters enormously.
"Firewalls serve as the primary barrier between trusted internal networks and untrusted external networks, monitoring and controlling incoming/outgoing traffic based on security rules to prevent unauthorized access, malware, and other threats."
Here is where many small businesses go wrong. They treat a firewall as a passive device rather than an active defense tool. A firewall with outdated rules, no monitoring, and no regular review is barely better than having none at all. Threats evolve constantly, and your firewall rules need to evolve with them.
Key reasons every small business needs a properly managed firewall:
- Access control: Restricts which users, devices, and applications can reach sensitive systems
- Threat blocking: Filters known malicious IP addresses, ports, and protocols before they reach your network
- Traffic visibility: Logs network activity so you can detect unusual patterns early
- Compliance support: Many industry regulations require documented perimeter security controls
- Cost efficiency: A well-configured firewall prevents incidents that cost far more to remediate than to prevent
The misconception that firewalls are outdated technology persists, but it is simply wrong. Modern firewalls have evolved far beyond basic packet filtering. They are intelligent, context-aware systems that remain foundational to any serious cybersecurity program.
Types of firewalls: Choosing the right protection for your business
With the basics covered, let's look at the various types of firewalls to see which ones best fit different business environments. Not every firewall is built the same, and choosing the wrong type for your environment can leave critical gaps.
Key firewall types include packet filtering, stateful inspection, Next-Generation Firewalls (NGFW), and proxy or web application firewalls (WAF). Each operates at different layers of the network and offers distinct levels of protection.
| Firewall type | OSI layers | Key strengths | Best for |
|---|---|---|---|
| Packet filtering | Layer 3 | Fast, lightweight, low cost | Basic perimeter control |
| Stateful inspection | Layers 3-4 | Tracks connection state, more accurate | General SMB perimeter |
| NGFW | Layers 3-7 | Deep packet inspection, IPS, app awareness | Complex or regulated environments |
| Proxy / WAF | Layer 7 | Application-level filtering, web protection | Web-facing apps, e-commerce |
Packet filtering is the oldest form. It checks packet headers for source and destination addresses and port numbers, then allows or blocks based on rules. It is fast but shallow. It cannot detect threats hidden inside legitimate-looking traffic.
Stateful inspection improves on this by tracking the state of active connections. It knows whether a packet is part of an established session or an unexpected intrusion attempt. This is the baseline for most small business perimeter firewalls today.
Next-Generation Firewalls are where the real power lies. NGFWs perform deep packet inspection (DPI), meaning they look inside the traffic itself, not just the headers. They include intrusion prevention systems (IPS), application awareness, and often integrate threat intelligence feeds. NIST SP 800-41 recommends NGFWs for complex environments and stateful firewalls for basic perimeter needs.

Proxy and WAF solutions operate at the application layer and are especially valuable for businesses running web-facing services. They inspect HTTP and HTTPS traffic for injection attacks, cross-site scripting, and other application-layer threats.
One important nuance: hardware firewalls excel at raw throughput and are ideal for on-premises environments with high traffic volumes. Cloud-managed firewalls trade some throughput for centralized management and easier scaling, which suits distributed teams or businesses with remote workers.
Pro Tip: Before selecting a firewall, map out your actual traffic volume, the number of remote users, and whether you have web-facing applications. Those three factors will tell you whether a stateful firewall is enough or whether you need an NGFW with DPI enabled.
Active management is essential. An unmanaged firewall, regardless of type, increases risk over time as rules become outdated and threat patterns shift.
How firewalls protect small businesses: Core functions and layered defense
Knowing the types, let's examine what firewalls actually do to keep your business secure and how to maximize their impact.
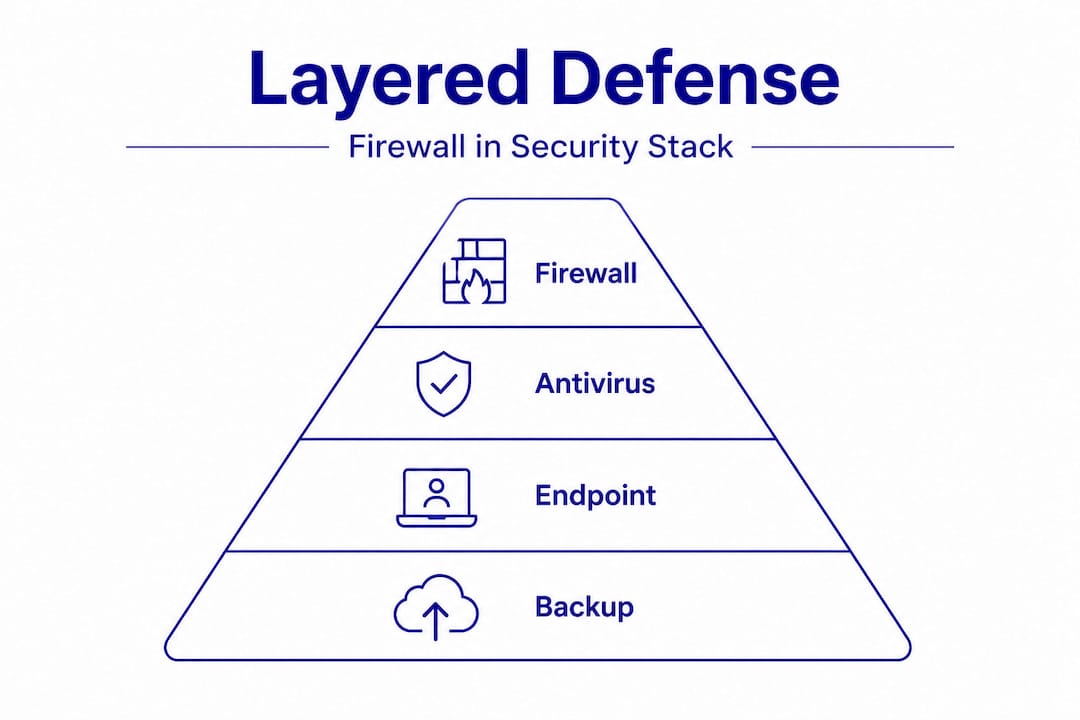
For small businesses, firewalls provide cost-effective protection through hardware, software, and SaaS options. They deliver ongoing monitoring and alerts, access control by IP address, port, and protocol, and virus and malware blocking. But they work best when paired with antivirus software as part of a layered defense.
Here is a practical breakdown of what a properly managed firewall does for your business day to day:
- Monitors all inbound and outbound traffic in real time, flagging anomalies before they become incidents
- Blocks unauthorized access attempts from external sources, including port scans, brute force attacks, and known malicious IPs
- Controls application usage by restricting which programs can communicate over the network
- Generates logs and alerts that give your IT team or managed service provider visibility into what is happening on your network
- Supports segmentation by enforcing rules between different parts of your internal network, not just at the perimeter
The table below shows how firewall protection layers compare in terms of what each layer stops:
| Security layer | Primary threats blocked | Works alone? |
|---|---|---|
| Firewall | Unauthorized access, port attacks, known malicious IPs | No |
| Antivirus | Malware, ransomware, phishing payloads | No |
| Endpoint detection | Behavioral threats, zero-days | No |
| Firewall + antivirus + EDR | Broad threat coverage | Yes, when combined |
This table makes the point clearly. No single tool is sufficient. A firewall stops threats at the network boundary, but once something slips through, antivirus and endpoint detection and response (EDR) tools are your next line of defense.
For businesses looking at IT and threat protection services, understanding this layered model is the starting point. You can also review critical security controls to see how firewalls fit within a broader framework of essential defenses.
The cost argument for firewalls is also compelling. A managed hardware firewall with ongoing support costs a fraction of what a single ransomware incident costs in downtime, recovery, and reputational damage. For small businesses with limited budgets, this is one of the highest-return investments in cybersecurity.
Manufacturing, OT, and the special demands of industrial firewalls
Manufacturing and operational technology present unique challenges, so let's explore how firewalls meet these demands.
Industrial environments introduce a layer of complexity that standard IT firewalls are not always equipped to handle. In a manufacturing facility, you are not just protecting computers and servers. You are protecting programmable logic controllers (PLCs), supervisory control and data acquisition (SCADA) systems, and a growing ecosystem of Industrial Internet of Things (IIoT) devices.
In manufacturing and OT environments, firewalls enable network segmentation using the Purdue model, which organizes industrial networks into distinct zones and a demilitarized zone (DMZ). This architecture prevents IT-to-OT lateral movement, meaning a threat that compromises your business network cannot automatically reach your production floor systems.
Key requirements for industrial firewalls include:
- Protocol support: Industrial firewalls must understand OT-specific protocols like Modbus, EtherNet/IP, and DNP3, not just standard TCP/IP
- Zone enforcement: Rules must enforce strict boundaries between IT zones (enterprise network) and OT zones (control systems, field devices)
- Legacy system protection: Many PLCs and SCADA systems run outdated operating systems that cannot be patched. Firewalls compensate by controlling what can reach them
- Minimal latency: Control loops in manufacturing are time-sensitive. Firewall processing overhead must not disrupt real-time operations
- Logging and alerting: Every connection attempt to OT assets should be logged for audit and incident response purposes
Understanding network segmentation strategies is critical for any manufacturer running connected equipment. Without proper segmentation enforced by industrial-grade firewalls, a single phishing email on the business network can become a production shutdown.
For businesses navigating cybersecurity compliance in manufacturing, firewall documentation and rule management are often required by regulators. And if you are building out your overall approach, the manufacturing network protection guide offers a practical starting point.
Pro Tip: Apply least privilege to every OT firewall rule. If a PLC only needs to communicate with one historian server, write the rule to allow exactly that and nothing else. Then enable logging on all OT zone rules so you have a full audit trail for compliance and incident response.
Nuances, pitfalls, and best practices in firewall management
To round out your understanding, let's address the critical pitfalls and proven practices for ongoing firewall management.
Even a well-chosen firewall can fail if it is not managed correctly. The most common issues are not technical failures. They are human ones: rules that were never cleaned up, changes made without testing, and configurations that were set once and forgotten.
Edge cases that trip up small businesses include rule preemption, where an earlier rule inadvertently blocks a later, more specific rule from ever being evaluated. They also include encrypted traffic inspection overhead, which can degrade performance if not sized correctly, and default-deny misconfigurations that accidentally allow all inbound traffic instead of blocking it.
Common firewall management pitfalls to watch for:
- Rule bloat: Firewall rule sets grow over time. Old rules for decommissioned systems stay in place, creating confusion and potential security gaps
- No change management: Making rule changes without documentation or testing can break legitimate services or open unintended access
- Ignoring logs: Firewalls generate valuable data. Not reviewing logs means threats can persist undetected for weeks or months
- Skipping encrypted traffic inspection: Many modern attacks travel over HTTPS. If your firewall is not inspecting encrypted traffic, it is missing a significant portion of the threat landscape
- OT performance impact: In industrial settings, enabling deep inspection on time-sensitive control traffic can disrupt operations. IEEE research has documented latency impacts on control loops from improper firewall configurations
The solution to most of these problems is a structured change management process. Before deploying any firewall rule change, simulate it in a test environment or use tools designed to evaluate firewall changes before deployment. This catches conflicts, performance issues, and unintended access grants before they affect production.
Reviewing segmentation best practices alongside your firewall rule review process will also help you identify zones that are under-protected or over-permissive.
Pro Tip: Schedule a formal firewall rule review every quarter. Treat it like a financial audit. Look for rules that have not been triggered in 90 days, rules without documentation, and any rules that allow broad inbound access. Each one is a potential risk waiting to be exploited.
Why the conventional wisdom about firewalls is incomplete
Most guides on firewalls tell you what they are and how to set them up. What they rarely address is the ongoing management gap that leaves most small businesses exposed long after installation.
Here is the uncomfortable reality: a firewall configured three years ago and never touched since is not protecting you the way you think it is. Threat actors have changed tactics. Your network has changed. New devices have been added. Old services have been retired. But the firewall rules often reflect none of that.
Active management is not optional. Unmanaged firewalls increase risk over time, not just because rules go stale, but because the absence of monitoring means you lose visibility into what is actually happening on your network. You cannot respond to threats you cannot see.
The other gap is the perimeter-only mindset. Many small businesses invest in a strong perimeter firewall and consider the job done. But modern attacks frequently originate from inside the perimeter, through phishing emails, compromised credentials, or infected USB drives. A perimeter firewall does nothing to stop lateral movement once a threat is already inside.
This is why NGFWs with internal segmentation capabilities, paired with endpoint protection and reviewed security controls, represent the actual standard of care. Not just a box at the edge of the network, but a set of enforced boundaries throughout it.
The businesses that avoid serious incidents are not necessarily the ones with the most expensive firewalls. They are the ones with actively managed, regularly reviewed, and properly integrated security tools. That is the standard worth aiming for.
How Symmetry Network Management helps you maximize firewall protection
Managing firewall rules, monitoring logs, and keeping up with evolving threats is a full-time responsibility. For most small businesses, that is not realistic without dedicated support.

Symmetry Network Management provides managed IT and cybersecurity services built specifically for small businesses in manufacturing, aerospace, and professional services. That includes firewall setup, ongoing rule management, 24/7 monitoring, and integration with layered defenses like endpoint security and backup solutions. Whether you are running a production floor with OT assets or a professional services firm with compliance requirements, Symmetry's team brings the expertise to keep your defenses current and your operations protected. Schedule a free assessment to identify gaps in your current firewall configuration and get a clear picture of where your security posture stands.
Frequently asked questions
What are the most common firewall mistakes small businesses make?
Misconfiguring rules, ignoring default-deny settings, and failing to actively manage firewalls are the most common errors. Rule preemption and default-deny misconfigs are particularly dangerous because they can silently allow all inbound traffic while appearing to be functional.
How often should firewall rules be reviewed by a small business?
Firewall rules should be reviewed at least quarterly and after any major network change or security incident. Unmanaged firewalls increase risk over time as outdated rules accumulate and threat patterns shift.
Is a firewall alone enough to protect against modern cyber threats?
No. Firewalls should be paired with antivirus and additional layered security tools for real protection. Pairing with antivirus for layered defense is the minimum standard for small businesses facing modern threats.
Should manufacturing businesses use specialized firewalls?
Yes. Industrial firewalls with support for OT protocols are necessary to properly protect PLC, SCADA, and IIoT assets. Standard IT firewalls lack support for industrial protocols like Modbus and cannot enforce the zone boundaries required in manufacturing environments.
Recommended
- Why use cybersecurity services: Essential protection for SMBs
- 5 Critical Security Controls Every Small Business Needs | Symmetry Network Management
- How to Secure Manufacturing Networks: A Practical SMB Guide | Symmetry Network Management
- Network Segmentation Best Practices | Symmetry Network Management
