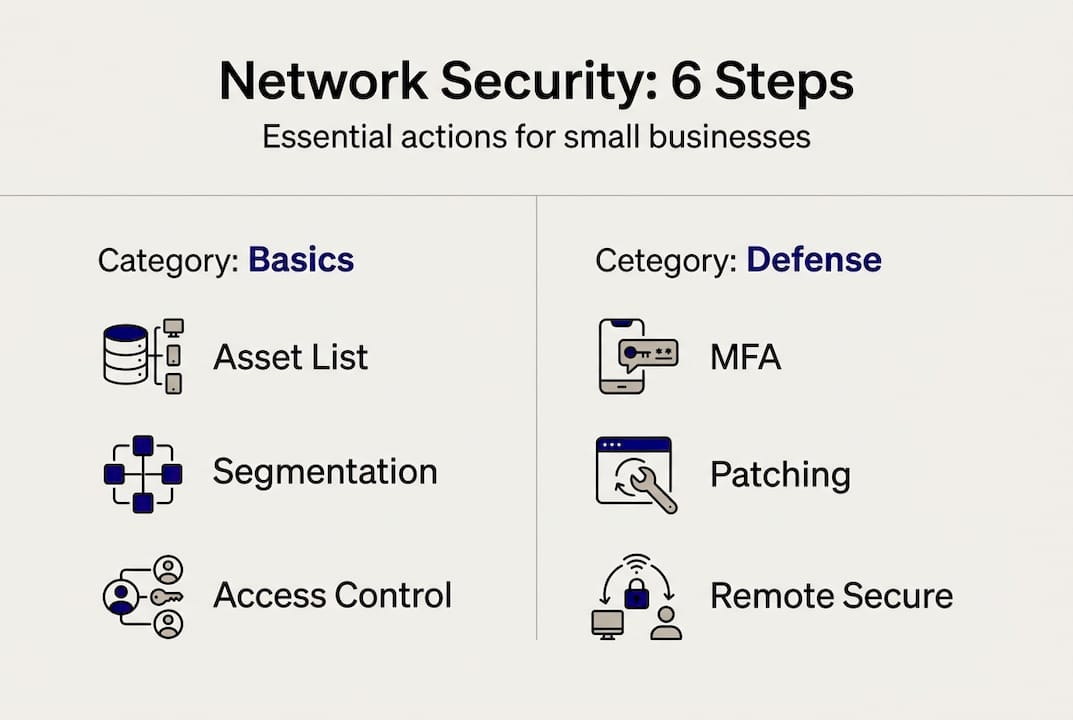
Small manufacturers, aerospace suppliers, and professional services firms are increasingly in the crosshairs of cybercriminals. A single misconfigured firewall or an unmonitored remote access point can expose customer data, halt production, and trigger costly compliance violations. Preventable misconfigurations remain a root cause of significant financial losses for small businesses. This guide walks you through six practical steps to close those gaps, covering everything from network segmentation and access controls to monitoring, patching, and safe remote access, whether you operate under strict defense contracts or simply need solid protection for your operations.
Table of Contents
- Assess your current network and prepare for improvements
- Segment networks to prevent lateral movement
- Strengthen access controls and enable multi-factor authentication
- Monitor, patch, and protect: essential daily defenses
- Limit internet exposure and secure remote access
- Why most small businesses struggle with network security (and what actually works)
- Protect your network with expert-managed solutions
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Segment your network | Divide IT from OT environments to limit hacker movement and meet compliance. |
| Enforce MFA everywhere | Multi-factor authentication blocks most breaches and is easy to deploy quickly. |
| Monitor and patch regularly | Centralized logging and timely updates stop threats before they do damage. |
| Limit internet exposure | Disconnect unnecessary devices and require VPN with MFA for any remote access. |
| Educate and plan | Consistent employee training and an incident plan greatly reduce cyber risks. |
Assess your current network and prepare for improvements
Before you can fix anything, you need a clear picture of what you have. Many small businesses discover they have shadow devices, forgotten cloud accounts, or unmanaged operational technology (OT) equipment running on the same network as office computers. That mix of IT and OT creates real risk.
Start by listing every device, system, and service your business uses. This includes computers, servers, PLCs, cloud storage, VPNs, and any vendor-connected equipment. Then, map each asset to the data it handles. Inventorying systems and assessing compliance requirements against NIST, CMMC, or CISA baselines is a foundational step that most small businesses skip, and it costs them later.
| Assessment area | Key questions to answer |
|---|---|
| Device inventory | Are all devices known, labeled, and managed? |
| Compliance framework | Does your work trigger CMMC, NIST SP 800-171, or CISA CPGs? |
| Cloud and remote access | Who can connect, and from where? |
| Data sensitivity | Where is confidential or regulated data stored? |
For aerospace and defense contractors, CMMC compliance requirements are non-negotiable. For general manufacturers and professional services, CISA's Cybersecurity Performance Goals provide a practical baseline. Free resources from the NIST small business community offer templates to get started quickly.
- Identify all IT and OT assets, including vendor-managed equipment
- Map compliance requirements to your contracts and industry
- Flag gaps using a simple spreadsheet or free NIST template
- Prioritize by risk level, not by ease of fix
Pro Tip: Before buying any new security tool, complete your asset inventory. You cannot protect what you cannot see, and most businesses already have free tools available that go unused. Reviewing the manufacturing network security guide can help you build a tailored starting checklist.
Segment networks to prevent lateral movement
Once you know your environment, the next big win is strategic network segmentation. Segmentation means dividing your network into separate zones so that if an attacker gets into one area, they cannot freely move to other systems. Think of it as fireproof doors inside a building.
For small manufacturers and aerospace suppliers, separating IT (office computers, email, accounting) from OT (PLCs, CNC machines, SCADA systems) is critical. The Purdue Model segmentation approach organizes industrial networks into numbered levels, keeping the most sensitive control systems isolated from general business traffic. This model has been validated across industrial sectors for reducing attack risk on operational systems.

| Segmentation method | Best for | Complexity |
|---|---|---|
| VLANs (virtual LANs) | Small IT/OT separation | Low to medium |
| Firewall zones | Departments, guest Wi-Fi | Medium |
| Physical separation | High-risk OT systems | Medium to high |
| Secure conduits | Cross-zone data transfer | Medium |
Review network segmentation best practices to match the right method to your budget and risk level. For most small businesses, starting with VLANs between office and shop-floor networks delivers the highest return for the lowest cost.
- Separate guest Wi-Fi from your corporate network immediately
- Isolate any internet-facing systems from internal production systems
- Use firewall rules to control traffic between segments
- Log all cross-segment traffic for review
Pro Tip: Start with your most critical asset, such as your production line controller or client file server, and segment that first. You do not need to rearchitect everything at once. Incremental segmentation still significantly reduces your exposure while you build toward a complete model with help from securing manufacturing networks resources.
Strengthen access controls and enable multi-factor authentication
With your network zones in place, secure who gets access and how they prove their identity. Weak access controls are where most breaches begin. Weak controls and absent phishing-resistant MFA are cited as the leading cause of successful cyberattacks across small and mid-size organizations.
Multi-factor authentication (MFA) requires users to verify their identity with two or more methods, such as a password plus a code sent to their phone. It is not a luxury. It is a baseline control that blocks the majority of credential-based attacks.
- Audit all user accounts and remove any that are inactive or no longer needed
- Enable MFA on every external-facing system, including email, VPN, and remote desktop tools
- Apply role-based access control so employees can only reach the systems their job requires
- Require strong, unique passwords and enforce this with a password manager
- Review admin and privileged accounts monthly to verify they are still necessary
The CISA guidance on MFA outlines which authentication types provide the strongest protection. Hardware security keys and authenticator apps beat SMS codes for high-risk accounts.
Learn how to roll out MFA best practices across your organization, even if you manage a small team without a dedicated IT staff.
Pro Tip: Start MFA rollout with privileged accounts and remote workers before expanding to everyone else. These accounts carry the most risk if compromised, and securing them first gives you immediate, measurable protection.
Monitor, patch, and protect: essential daily defenses
Robust access controls set the perimeter. Now, let's keep the heart of your network healthy every day. Monitoring and patching are the two most underfunded and underperformed activities in small business IT, and they are exactly where attackers look for opportunity.
Centralized logging and consistent patching are required for CMMC Level 2 and are also the most reliable early warning system for any organization. Logging captures what happens on your network so you can detect unusual behavior before it becomes a crisis.
| Tool | Purpose | Cost |
|---|---|---|
| Logging Made Easy (CISA) | Centralized log collection for IT | Free |
| Malcolm | OT and industrial network traffic analysis | Free |
| Windows Event Viewer | Basic endpoint log review | Built-in |
| Managed SIEM | Automated alerting and correlation | Subscription |
"CMMC Level 2 requires 110 controls for protecting controlled unclassified information in aerospace and defense supply chains. Employee awareness training is among the strongest predictors of overall defense success."
Here is a realistic maintenance schedule for small businesses:
- Daily: Review flagged alerts from monitoring tools; verify backup completion
- Weekly: Apply critical patches to operating systems and software; review user access logs
- Monthly: Run vulnerability scans; conduct a short employee security awareness refresher; review the incident response plan
Review the key security controls your business should have in place, and consider how outsourcing monitoring to a managed provider removes the burden of 24/7 oversight from your internal team.
Limit internet exposure and secure remote access
Protecting your network's perimeter also means limiting which doors are open to the outside world. Many small manufacturing and aerospace businesses have systems that are internet-accessible without their knowledge, left open during a quick vendor setup or forgotten after a project ended.
Systems commonly exposed to the internet without proper controls include:
- Remote desktop protocol (RDP) ports left open on servers
- Older VPN appliances with unpatched vulnerabilities
- Web-based admin panels for routers or switches
- OT devices connected directly to the internet for vendor monitoring
- Cloud storage with overly permissive sharing settings
"Remote access to OT systems should be restricted and enabled only when necessary, always protected by VPN and multi-factor authentication. Openly accessible industrial systems are among the most targeted assets in the threat landscape."
Follow these steps to reduce your internet exposure:
- Run a free port scan using Shodan or CISA's scanning service to find exposed services
- Disable any RDP, admin panels, or legacy protocols that do not need to be internet-facing
- Replace direct connections with a VPN requiring MFA for all remote access
- Work with vendors to limit their access to scheduled windows with logging enabled
- Document every external connection point and review the list quarterly
ITAR and AS9100 solutions for aerospace firms often require these controls as part of contract compliance. The CISA OT remote access advice gives specific, step-by-step direction for small industrial operations.
Pro Tip: Run a free external scan of your public IP address at least once per quarter. You may be surprised what is visible. Finding an open port before an attacker does is one of the highest-value, lowest-cost actions you can take.
Why most small businesses struggle with network security (and what actually works)
Here is an uncomfortable truth: most small businesses that check every box on a compliance framework still get breached. Not because the frameworks are wrong, but because completing a checklist once does not protect you next month when an employee clicks a phishing link or a vendor leaves a port open.
The real failures we see consistently come down to three things: no follow-through on training, infrequent reviews of access and configurations, and tactics that do not evolve as threats do. A compliance audit is a snapshot. Attackers work in real time.
For most small businesses, a disciplined set of core basics, applied consistently, beats a complex framework applied inconsistently. Segmentation, MFA, patching, logging, and limited internet exposure are not advanced concepts. They are the foundation, and skipping any one of them creates a gap that sophisticated attackers will find.
The question of when to outsource versus build in-house comes down to one honest question: does your team have the time and expertise to monitor, respond, and improve every single month? If not, a managed provider fills that gap more reliably than hiring alone. Read more practical network security insights on what works in the field for businesses like yours.
Protect your network with expert-managed solutions
If you're ready to turn these principles into a secure, compliant network, Symmetry Network Management can help you get there without building an internal IT department from scratch.

Symmetry Network Management delivers tailored managed IT services for small businesses in manufacturing, aerospace, and professional services. From network segmentation and MFA deployment to 24/7 monitoring and compliance preparation, the team handles the technical heavy lifting so you can focus on running your business. Explore network segmentation help specific to your environment, and review the small business security controls Symmetry recommends as a starting point. Schedule a free security assessment today to identify your most urgent gaps and get a clear action plan.
Frequently asked questions
What are the top three actions to improve network security fast?
Segmentation and MFA are core early steps in CISA and NIST guidance, and removing unnecessary internet exposure rounds out the three most impactful quick wins. Prioritizing these three controls addresses the majority of common attack vectors.
How do you secure OT networks in a small manufacturing environment?
The Purdue Model and secure conduits are recommended by CISA and NIST for isolating operational systems. Apply VLANs or subnets, restrict remote access, and monitor all OT traffic for anomalies as your baseline.
What is the most common weakness leading to breaches?
MFA absence is a root cause in many breaches according to NIST and CISA analysis. The absence of phishing-resistant multi-factor authentication remains the single most exploitable gap in small business environments.
How often should network security be reviewed or updated?
Regular management, patching, and reviews are central to CISA and NIST guidance. Security policies, employee training, and software patching should be addressed at least monthly for consistent protection.
Can SMBs outsource network security management?
CISA and NIST recommend outsourcing when in-house expertise is limited. Outsourcing is both cost-effective and a reliable path to maintaining compliance and response capability without a full internal IT team.
Recommended
- 5 Critical Security Controls Every Small Business Needs | Symmetry Network Management
- How to Secure Manufacturing Networks: A Practical SMB Guide | Symmetry Network Management
- Top 10 IT Infrastructure Mistakes Small Businesses Make - Symmetry Network Management
- Securing Microsoft 365 for Small Business | Symmetry Network Management
- Effective Ways to Improve Network Security for Brisbane SMEs - IT Start
