Small manufacturers often operate under the assumption that cybercriminals are focused on larger, more visible targets. That assumption is dangerously wrong. Unsophisticated cyber actors are actively exploiting weak operational technology (OT) environments in manufacturing facilities across the U.S., often with minimal technical skill. The consequences range from production shutdowns to regulatory penalties and lost contracts. This article breaks down the real threat landscape for small manufacturers, explains what compliance actually requires, and gives you a practical path forward to strengthen your IT security without overwhelming your team or your budget.
Table of Contents
- Why small manufacturers are bigger cyber targets than you think
- Compliance realities: Why security isn't optional for manufacturers
- Top frameworks and controls: How to prioritize IT security efforts
- Simple steps to boost IT security (without blowing your budget)
- A common trap: Overcomplicating IT security in small manufacturing
- Next steps: How our team helps small manufacturers stay secure
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| No business is too small | Attackers actively target small manufacturers, often exploiting easy-to-fix weaknesses. |
| Compliance drives action | Meeting CMMC and NIST standards is mandatory for DoD supply chain manufacturers, with heavy penalties for non-compliance. |
| Frameworks simplify security | NIST CSF and CISA CPGs help set practical IT security priorities for small manufacturers. |
| Start with simple fixes | Actions like keeping OT offline and enabling MFA block most threats and fit modest budgets. |
Why small manufacturers are bigger cyber targets than you think
The "too small to hack" mindset is one of the most persistent and costly myths in manufacturing. Attackers are not always sophisticated, and they do not always go after the biggest fish. They go after the easiest targets. Small manufacturers frequently run aging equipment connected to modern networks, creating a gap that attackers exploit with basic tools and publicly available techniques.
OT systems are increasingly targeted due to outdated security configurations and internet exposure. Many of these systems were designed decades ago, long before cybersecurity was a consideration. They were built to run reliably, not securely. When those systems get connected to the internet for remote monitoring or supply chain integration, they become entry points that attackers can find with simple scanning tools.
Here is a snapshot of the most common attack types hitting small manufacturers right now:
| Attack type | How it works | Potential impact |
|---|---|---|
| Ransomware | Encrypts files and halts operations | Production downtime, ransom costs |
| Phishing | Tricks employees into sharing credentials | Data theft, network access |
| Supply chain compromise | Targets vendors to reach larger networks | Loss of contracts, liability |
| OT exploitation | Targets unpatched industrial control systems | Equipment damage, safety risks |
Beyond the attack types, consider what makes small manufacturers uniquely exposed:
- Limited IT staff: Most small manufacturers rely on one generalist or an outsourced provider with limited manufacturing expertise.
- Legacy systems: Equipment running Windows XP or older programmable logic controllers (PLCs) cannot receive modern security patches.
- Flat networks: IT and OT systems often share the same network, meaning one compromised laptop can reach the factory floor.
- Vendor access: Remote access granted to equipment vendors is rarely monitored or restricted properly.
"A single unpatched OT device connected to the internet can give an attacker a foothold into your entire operation. The barrier to entry for these attackers is lower than most manufacturers realize."
Reviewing your manufacturing network security guide is a smart first step to understanding your exposure. Many of the most damaging breaches in manufacturing started with a basic lapse, such as a default password left unchanged or a remote desktop port left open. Avoiding common IT infrastructure mistakes can close those gaps before attackers find them.
Compliance realities: Why security isn't optional for manufacturers
Understanding the threat is only one side of the equation. The other is the regulatory pressure that comes with operating in today's manufacturing environment, especially if you work with the U.S. Department of Defense (DoD).

Small manufacturers must comply with the Cybersecurity Maturity Model Certification (CMMC) and NIST SP 800-171 for any defense-related work, with no size exemption and significant associated costs. This is not a guideline or a best practice. It is a contract requirement. If you handle Controlled Unclassified Information (CUI) as part of a DoD supply chain, you must meet these standards or risk losing your contract eligibility.
Here is how the major frameworks compare:
| Framework | Who it applies to | Key focus | Certification required? |
|---|---|---|---|
| CMMC Level 1 | All DoD contractors | Basic cyber hygiene (17 practices) | Self-assessment |
| CMMC Level 2 | Handlers of CUI | 110 NIST SP 800-171 controls | Third-party assessment |
| NIST CSF 2.0 | Any manufacturer | Risk-based security framework | No |
| ISO 27001 | Internationally active firms | Information security management | Yes |
The consequences of ignoring these requirements follow a clear and painful progression:
- Contract loss: DoD primes are required to verify subcontractor compliance. Non-compliant suppliers get removed from consideration.
- Legal exposure: Submitting a false self-assessment is considered a False Claims Act violation, which carries severe financial penalties.
- Breach liability: Without required controls, a breach can expose you to customer lawsuits and regulatory fines.
- Reputational damage: Word travels fast in tight-knit manufacturing supply chains. One publicized breach can cost you future bids.
The cost of compliance is real, but it is far lower than the cost of non-compliance. Assessments, remediation, and managed security services are predictable, budgetable expenses. A ransomware attack or contract termination is not.
Pro Tip: Start your compliance journey by requesting a System Security Plan (SSP) template from your local Manufacturing Extension Partnership (MEP) center. It gives you a structured way to document your current controls before you begin gap analysis.
For manufacturers working in regulated environments, a solid cybersecurity compliance guide can help clarify what documentation and controls are required before your next assessment.
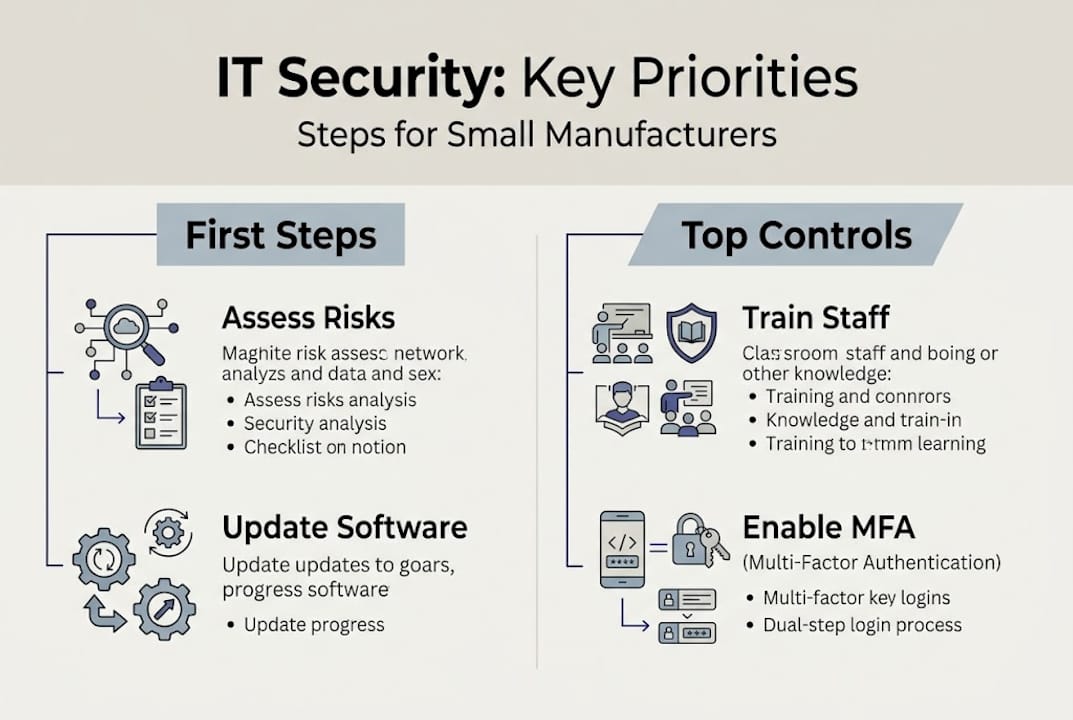
Top frameworks and controls: How to prioritize IT security efforts
With compliance requirements clarified, the practical question becomes: where do you start? The good news is that you do not need to build a security program from scratch. Established frameworks give you a tested blueprint.
NIST CSF 2.0 and CISA Cross-Sector Cybersecurity Performance Goals (CPGs) offer prioritized, practical controls designed for environments like yours, including mixed IT and OT settings. These frameworks are not just for large enterprises. They were specifically designed to be scalable.
Here is how the top controls map to manufacturing environments:
| Control | IT application | OT application | Cost level |
|---|---|---|---|
| Network segmentation | Separate office and production networks | Isolate PLCs and SCADA systems | Low to medium |
| Multi-factor authentication (MFA) | Email, VPN, remote access | Vendor remote access | Low |
| Patch management | Workstations and servers | Firmware updates where supported | Low |
| Asset inventory | Track all devices on the network | Catalog all OT/ICS equipment | Low |
| Incident response plan | Define roles and escalation paths | Include OT shutdown procedures | Low |
The controls that offer the highest value for the least investment are almost always the basics:
- MFA on all remote access: This single control blocks the majority of credential-based attacks.
- Network segmentation: Keeping your office network separate from your production floor limits how far an attacker can move if they get in.
- Regular patching: Most ransomware exploits known vulnerabilities that already have patches available.
- Backups with tested recovery: A verified backup means a ransomware attack becomes a disruption, not a disaster.
People and process matter as much as technology here. A firewall does nothing if an employee clicks a phishing link and hands over their credentials. Training staff to recognize suspicious emails, verify unusual requests, and report incidents quickly is a control in itself.
Pro Tip: Map your current practices against the critical security controls list before investing in new tools. You may already have more coverage than you think, and the gaps will become obvious quickly.
Simple steps to boost IT security (without blowing your budget)
With a clear framework in place, small manufacturers can take practical action starting today. These steps are ordered by impact and ease of implementation.
- Build an asset inventory: You cannot protect what you do not know you have. List every device on your network, including printers, PLCs, and any equipment with a network connection. Free tools like network scanners can help automate this.
- Enable MFA everywhere possible: Start with email, VPN, and any remote access tools. Most platforms support MFA at no additional cost. This is the single highest-return security action available.
- Segment your network: Work with your IT provider to create separate network zones for office systems and production equipment. Even a basic VLAN setup reduces your attack surface significantly.
- Patch on a schedule: Set a monthly patching schedule for all workstations and servers. For OT systems that cannot be patched, document the risk and compensate with network isolation.
- Train your team quarterly: Brief, focused sessions on phishing recognition and safe password practices are more effective than annual all-day training events.
- Test your backups: Run a restore drill at least twice a year. A backup you have never tested is a backup you cannot trust.
- Restrict vendor access: Require vendors to use a dedicated, monitored remote access solution rather than open RDP ports. Disable access when it is not actively needed.
Basic mitigations like keeping OT offline, enabling MFA, and timely patching can block most attacks, even from unsophisticated hackers. That is not a minor claim. It means the majority of the risk you face today can be addressed with steps that cost very little.
"Most manufacturers we speak with are not far from a solid security baseline. The gap is usually awareness and consistency, not budget."
For teams using cloud productivity tools, reviewing Microsoft 365 security tips can uncover quick wins in your existing environment. And if you want a deeper look at your network posture, the secure manufacturing networks resource walks through architecture decisions specific to the manufacturing floor.
Pro Tip: Tackle one step per month rather than trying to implement everything at once. Consistent progress over six months will put you ahead of most small manufacturers in your industry.
A common trap: Overcomplicating IT security in small manufacturing
After years of working with small manufacturers, one pattern stands out clearly. Many business owners invest in expensive security tools and then underinvest in the habits and processes that make those tools effective. A next-generation firewall configured by someone who does not understand your environment provides less protection than a basic firewall managed consistently by someone who does.
80% of cybersecurity is non-technical, with people and processes mattering most, especially as OT and IT environments converge on the shop floor. That statistic should reframe how you think about your security budget. Spending on staff awareness, documented procedures, and routine reviews often moves the needle more than the next software purchase.
The IT/OT convergence happening in manufacturing today creates a unique cultural challenge. Production staff and IT staff often operate in silos, with different priorities and different risk tolerances. Bridging that gap requires leadership commitment, not just technology. When your team understands why people and process matter as much as tools, and when network segmentation insights are applied with operational context, the results are far more durable.
The manufacturers who build lasting security programs are not the ones with the biggest budgets. They are the ones who make security a routine part of how they operate every day.
Next steps: How our team helps small manufacturers stay secure
If this article has surfaced questions about where your operation stands, that is exactly the right reaction. Security gaps in manufacturing are common, and identifying them early is far less costly than discovering them after an incident.

At Symmetry Network Management, our managed IT services are built specifically for small manufacturers who need reliable, compliant, and affordable IT support. We offer a free security assessment to identify your most pressing gaps and map a realistic path forward. Our team understands both the IT and OT sides of manufacturing environments, and we work at a fixed, predictable price. Review our critical security controls overview to see where your operation may need attention, or contact our experts to schedule your assessment today.
Frequently asked questions
What are the most common cyber threats faced by small manufacturers?
Small manufacturers are increasingly targeted by ransomware, phishing, and attacks on OT systems due to weak or outdated protections. OT systems face higher targeting because legacy technology and limited security controls make them easier to exploit.
Is my business required to comply with CMMC or NIST standards?
If you supply to the U.S. Department of Defense, you are required to meet CMMC and NIST SP 800-171 standards, regardless of company size. CMMC and NIST requirements apply to all manufacturers handling DoD contracts with no size exemption.
How can I improve my IT security with a limited budget?
Focus on basic steps like keeping OT offline, enabling multi-factor authentication, training staff, and regularly updating software for strong results. Basic mitigations block most attacks, even when resources are limited.
What is the difference between CMMC and NIST SP 800-171?
CMMC builds on NIST SP 800-171 by adding certification and assessment requirements for defense suppliers. CMMC Level 2 incorporates all 110 NIST SP 800-171 controls plus a formal third-party assessment process.
Recommended
- How to Secure Manufacturing Networks: A Practical SMB Guide | Symmetry Network Management
- Symmetry Network Management | Managed IT Services
- 5 Critical Security Controls Every Small Business Needs | Symmetry Network Management
- El Monte IT Services - ITAR and AS9100 Managed IT Solutions
- Quality Assurance: 30% Defect Reduction & Cost Savings