Cyber hygiene is not a buzzword reserved for large enterprise IT teams. It refers to the routine habits and baseline practices that keep your systems, data, and people protected from the most common threats. Yet most SMBs underinvest in these basics, leaving them exposed to attacks that could have been prevented. For small businesses in manufacturing, aerospace, and professional services, the stakes are especially high. Regulated data, proprietary designs, and client records are all on the line. This article explains what cyber hygiene means, cuts through the myths, and gives you practical steps to build a stronger security foundation starting today.
Table of Contents
- Defining cyber hygiene: The basics and the myths
- Core elements of cyber hygiene for small businesses
- Standards and frameworks: Making cyber hygiene actionable
- Cyber hygiene challenges and sector-specific edge cases
- Why most small businesses miss the mark on cyber hygiene
- Take the next step: Strengthen your cyber hygiene
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Cyber hygiene is foundational | It involves consistent, basic cybersecurity practices any business can implement, not just complex tools for IT experts. |
| Focus on the essentials first | Patch software, use multi-factor authentication, train staff on phishing, and back up data regularly for maximum impact. |
| Use frameworks for guidance | Follow standards like NIST CSF and CISA CPGs to build repeatable, auditable cyber hygiene processes. |
| Tailor for your sector | Manufacturing and aerospace firms must address OT and supply chain risks; professional services should emphasize data and phishing protections. |
| Ongoing effort yields results | Sustained staff involvement and repeated review make basic protections effective against most cyber threats. |
Defining cyber hygiene: The basics and the myths
Cyber hygiene is best understood as the set of consistent, repeatable actions your business takes to maintain the health of its digital environment. Think of it the way you think of physical hygiene: skip it long enough, and problems compound quickly. The same logic applies to your IT systems.
Many small business owners assume that having antivirus software installed means they are covered. That is one of the most common and dangerous myths in cybersecurity. Antivirus is one layer, not a complete defense. Another misconception is the "set it and forget it" mindset: the idea that once you configure a firewall or enable a security feature, your job is done. Threats evolve. Your defenses need to as well.
So what does cyber hygiene actually include? The core mechanics include software patching, strong passwords with multi-factor authentication (MFA), antivirus and firewalls, regular backups, network segmentation, employee phishing training, and continuous monitoring. Each of these plays a distinct role in reducing your attack surface.
Here is the key reframe that matters for small businesses: cyber hygiene is a high-impact, low-complexity floor, not a full security program. You do not need to invest in enterprise-grade threat hunting tools to get meaningful protection. You need to execute the basics consistently.
"Cyber hygiene is about building the right habits into your daily operations, not about achieving perfection. The floor matters more than the ceiling for most small businesses."
The businesses that struggle most with securing manufacturing networks are often not missing advanced tools. They are missing consistent basics: unpatched systems, weak passwords, no staff training. That is a solvable problem.
Pro Tip: Before investing in any new security technology, audit your current basics. Are systems patched? Are staff trained on phishing? Are backups tested? Fixing gaps here delivers more protection per dollar than most advanced tools.
Core elements of cyber hygiene for small businesses
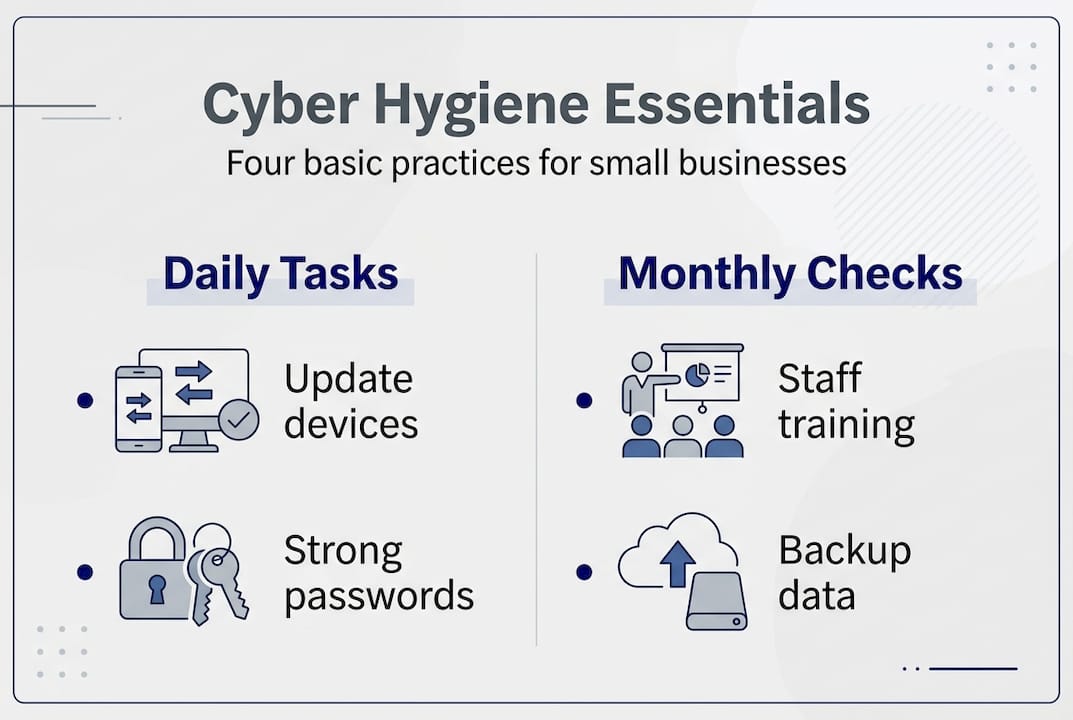
With the myths cleared up, here is what cyber hygiene looks like in practice. CISA identifies four essentials for SMBs: phishing training, MFA, software updates, and regular backups. These are the starting point, not the finish line.
| Hygiene essential | Business value | Primary risk mitigated |
|---|---|---|
| Software patching | Closes known vulnerabilities | Ransomware, exploits |
| Multi-factor authentication | Blocks credential theft | Account takeover |
| Employee phishing training | Reduces human error | Email-based attacks |
| Regular data backups | Enables fast recovery | Ransomware, data loss |
| Antivirus and endpoint security | Detects known malware | Malware, spyware |
| Network segmentation | Limits breach spread | Lateral movement |
| Firewall management | Controls traffic flow | Unauthorized access |
Here is a practical order for implementing these essentials if you are starting from scratch:
- Enable MFA on all business accounts, starting with email and remote access tools. The role of MFA in blocking credential attacks is well established and this step costs little to nothing on most platforms.
- Patch and update systems on a defined schedule. Weekly for critical systems, monthly for lower-priority endpoints. Do not wait for vendors to push updates automatically.
- Run phishing awareness training at least quarterly. Simulated phishing tests help staff recognize real attacks. Phishing awareness training is one of the highest-return investments a small business can make.
- Set up and test backups. Backups only matter if they work. Test restoration at least quarterly.
- Review and tighten network segmentation. Keep operational systems separate from office networks. Network segmentation limits how far an attacker can move if they get in.
- Deploy endpoint security across all devices, including employee laptops and mobile devices used for work.
One resource worth knowing: CISA's CyHy program offers free vulnerability scanning for small businesses. This scan identifies unpatched systems, misconfigurations, and open ports before attackers do. It is a no-cost starting point that many SMBs overlook entirely.
Standards and frameworks: Making cyber hygiene actionable
Habits are only sustainable when they are tied to a process. That is where frameworks come in. They give you a repeatable structure, an audit trail, and a common language for talking about security with partners, customers, and regulators.
The NIST Cybersecurity Framework 2.0 is the most widely used reference for U.S. manufacturers and aerospace suppliers. It maps cyber hygiene to six functions: Govern, Identify, Protect, Detect, Respond, and Recover. Each of your hygiene practices fits into one or more of these functions, making it easy to see gaps and prioritize action.
CISA's Cross-Sector Cybersecurity Performance Goals (CPGs) complement NIST by defining prioritized baseline controls for organizations operating in critical infrastructure sectors, which includes most manufacturing and aerospace SMBs. The CPGs are designed to be achievable, even with limited resources.
Key CISA CPG baseline controls relevant to SMBs:
- Implement MFA on all remote access and privileged accounts
- Maintain an inventory of software and hardware assets
- Establish and test an incident response plan
- Enforce strong password policies with a password manager
- Apply patches within defined timeframes based on risk level
- Train all staff on phishing and social engineering
| Framework | Primary focus | Strengths | SMB relevance |
|---|---|---|---|
| NIST CSF 2.0 | Broad cybersecurity lifecycle | Structured, widely accepted | High, especially for compliance |
| CISA CPGs | Baseline controls for critical sectors | Prioritized, achievable | High, designed for resource-limited orgs |
For businesses needing to meet NIST framework compliance requirements, aligning your hygiene practices with these frameworks is not extra work. It is the most efficient path to both security and audit readiness.
Cyber hygiene challenges and sector-specific edge cases
Applying frameworks in theory is one thing. Putting them into practice inside a small manufacturing plant, an aerospace supplier, or a busy professional services office is another. Each environment carries its own obstacles.
The most common barriers are skills gaps, tight budgets, and legacy systems that were never designed with cybersecurity in mind. An older CNC machine or a 15-year-old ERP system may not accept patches the same way a modern laptop does. Small organizations struggle most with patching and MFA implementation, particularly in operational technology (OT) environments.
OT and industrial control systems (ICS) in manufacturing and aerospace require a different approach. Air-gapping and ICS-specific patching are often necessary, but they create tradeoffs in connectivity and update frequency. Supply chain risks add another layer: a vendor with weak hygiene can become your vulnerability.
Professional services firms face different pressures. Phishing and credential theft are the top vectors. Role-based access controls, where staff can only access the data they need for their job, significantly reduce the damage a single compromised account can cause.
Top three sector-specific edge cases and practical mitigations:
- Legacy OT systems that cannot be patched: Isolate them on a dedicated network segment and monitor traffic closely for anomalies.
- Supply chain vendor access: Require vendors to meet basic hygiene standards before granting network access. Audit their access regularly.
- Remote or hybrid work in professional services: Enforce MFA on all remote sessions and deploy endpoint detection on every device that touches company data.
Pro Tip: Involve staff from operations, not just IT, when reviewing your cyber hygiene practices. Many vulnerabilities start on the shop floor or at the front desk, not inside the server room. A technician plugging in an unauthorized USB drive or an admin clicking a phishing link can bypass even well-configured practical network security steps.
Why most small businesses miss the mark on cyber hygiene
After working with small businesses across manufacturing, aerospace, and professional services, the pattern is consistent. The failure is rarely technical. It is cultural and procedural.
The biggest mistake is treating cyber hygiene as a one-time checklist. A business completes an assessment, implements recommendations, and then assumes the work is done. Six months later, systems are unpatched, staff have never been retrained, and the threat landscape has shifted. SMBs underinvest in basic practices not because they cannot afford them, but because there is no system for revisiting them.
Technology helps, but automation alone does not solve the problem. Automated patch management is only effective if someone is reviewing what got patched and what did not. Backup systems run silently until the day you need them, and by then it is too late to discover they were misconfigured.
The businesses that do this well treat cyber hygiene as an ongoing operational rhythm. They schedule quarterly reviews of their must-have security controls, run regular phishing simulations, and make security part of onboarding for every new hire. They spend less on incident response because they invest consistently in prevention. Staff engagement and leadership buy-in matter more than the size of the security budget.
Take the next step: Strengthen your cyber hygiene
Maintaining consistent cyber hygiene on your own is difficult, especially without a dedicated IT team. Threats change, systems age, and staff turnover creates gaps that are easy to miss.

Symmetry Network Management helps small businesses in manufacturing, aerospace, and professional services close those gaps with managed IT services that cover 24/7 monitoring, endpoint security, patch management, and compliance support. Our team works as your trusted IT partner, ensuring your hygiene practices stay current and your systems stay protected. Start with our free security assessment to identify where your gaps are today. Explore our guide to essential small business security controls for a practical next step.
Frequently asked questions
What are the most important cyber hygiene steps for a small manufacturing business?
Focus on regular software updates, strong passwords with multi-factor authentication, employee phishing training, and reliable data backups. These four SMB essentials from CISA form the baseline every manufacturing business should have in place.
How does cyber hygiene benefit professional services firms?
It protects sensitive client data from phishing, malware, and credential theft, reducing downtime and reputational risk. Phishing and credential attacks are the top threats for professional services, making MFA, training, and patching especially critical.
What free tools does the US government offer for improving cyber hygiene?
Small businesses can access free vulnerability scanning and cyber hygiene resources from CISA, including the CyHy program. These free scanning services help identify unpatched systems and misconfigurations before attackers exploit them.
Are cyber hygiene practices required for compliance (e.g., NIST, DFARS)?
Yes, cyber hygiene forms the foundation for NIST, DFARS, and other compliance standards in manufacturing and aerospace. Implementing CPGs for compliance with DFARS and NIST 800-171 requirements starts with getting the baseline hygiene practices right.
Recommended
- 5 Critical Security Controls Every Small Business Needs | Symmetry Network Management
- Symmetry Network Management | Managed IT Services
- Top 10 IT Infrastructure Mistakes Small Businesses Make - Symmetry Network Management
- 21 CFR Part 11 Cybersecurity Compliance Guide | Symmetry Network Management
- Cosa Sono I Rischi Cyber: Guida Essenziale 2024 - Security Hub