One compromised laptop on your shop floor or in your aerospace supply chain can expose controlled technical data, trigger regulatory fines, and cost you a government contract. Many small manufacturers and aerospace suppliers still treat endpoint security as an afterthought, assuming a basic antivirus program is enough. It is not. This guide breaks down what endpoint security actually means, which controls matter most, how compliance frameworks like CMMC and NIST 800-171 connect to device-level protection, and what practical steps your business can take to close the gaps before an incident forces your hand.
Table of Contents
- What is endpoint security?
- Core controls and technologies in endpoint security
- Compliance frameworks and endpoint security requirements
- Special challenges: BYOD, IoT, and unmanaged endpoints
- Device-level protection versus network security: Why both matter
- Our perspective: The compliance clock is already ticking
- Protect your endpoints with Symmetry Network Management
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Endpoints are prime targets | Desktops, laptops, and IoT systems are often entry points for threats in industrial supply chains. |
| Layered security is essential | Combining antivirus, EDR, firewalls, and encryption protects against a range of cyber risks. |
| Compliance needs device controls | Meeting standards like CMMC requires robust endpoint controls for data and eligibility. |
| BYOD and IoT pose challenges | Unmanaged devices and smart equipment require special strategies to secure. |
| Network and device security work together | Strong endpoint protection must complement, not replace, network safeguards. |
What is endpoint security?
Having recognized why small businesses cannot ignore the consequences of unsecured devices, let's clarify what endpoint security actually means and what it covers.
An endpoint is any computing device that connects to your business network. That includes the obvious ones like desktops, laptops, and servers, but also smartphones, tablets, and the shop-floor controllers running your CNC machines or quality inspection systems. In manufacturing and aerospace, the attack surface is wider than most owners realize because operational technology and information technology increasingly share the same network.
Endpoint security refers to the set of controls, policies, and technologies applied to individual computing devices to protect them from threats, unauthorized access, and data loss. It is not the same as securing your network perimeter with a firewall. A firewall watches traffic coming in and out. Endpoint security watches what is happening on the device itself.
This distinction matters enormously for businesses with importance in manufacturing concerns. A threat actor who slips past your perimeter firewall through a phishing email still encounters endpoint controls if they are properly configured. Without those controls, the attacker moves freely.
Common misconceptions include:
- Believing antivirus alone equals endpoint security
- Assuming cloud-hosted data removes endpoint risk
- Thinking network firewalls protect individual devices
- Overlooking endpoint protection for aerospace environments where embedded controllers are rarely patched
"Endpoint security is the foundation of any serious data protection and compliance strategy. Without it, every other security investment is built on sand." Every device that touches your network is a potential entry point, and each one requires deliberate, layered protection.
If your business handles controlled unclassified information (CUI) or sensitive technical drawings, understanding endpoint risks in Microsoft 365 environments is especially critical, since cloud productivity tools do not automatically secure the devices accessing them.
Core controls and technologies in endpoint security
Now that endpoint security is defined, let's break down the toolkit that actually keeps your endpoints and by extension your business secure.
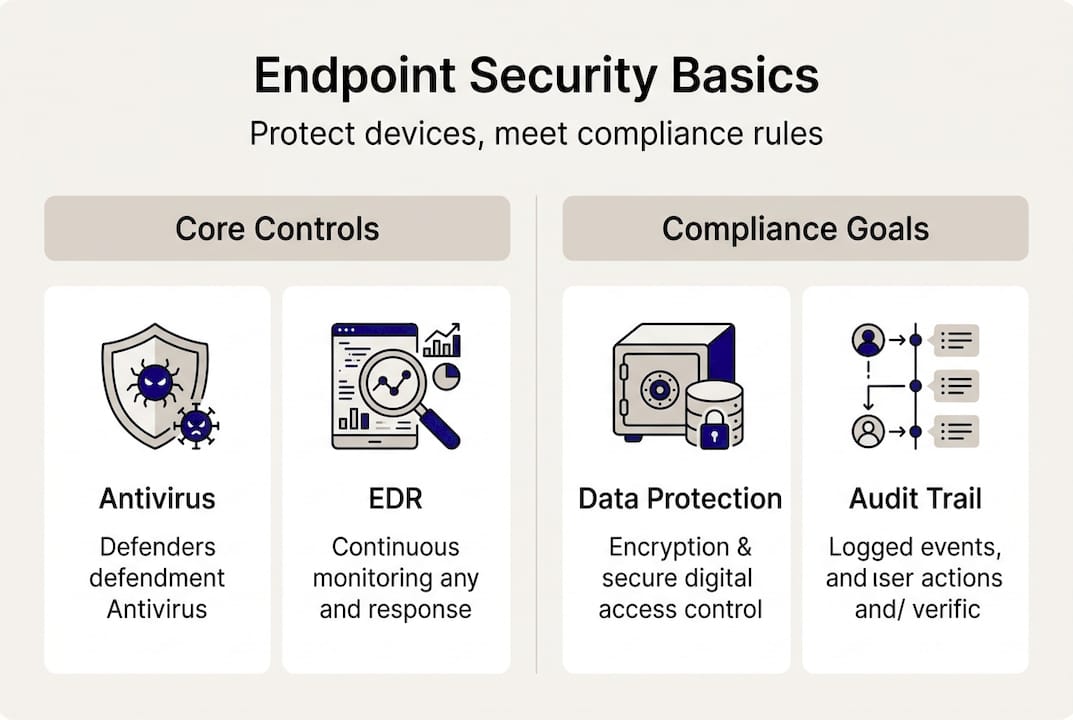
Endpoint security is not a single product. It is a layered set of controls, each addressing a different type of threat. Layered controls include antivirus, EDR, host-based firewalls, data loss prevention (DLP), encryption per NIST SP 800-111, patch management, and privileged access management (PAM). Here is how the main controls compare:

| Control | Function | Why it matters |
|---|---|---|
| Antivirus/Anti-malware | Detects known threats via signatures and heuristics | First line of defense against common malware |
| EDR (Endpoint Detection and Response) | Monitors behavior, detects anomalies, enables response | Catches unknown and fileless threats |
| Host-based firewall | Controls inbound/outbound traffic at device level | Limits exposure even on internal networks |
| DLP (Data Loss Prevention) | Blocks unauthorized data transfers | Protects CUI and proprietary designs |
| Encryption | Renders data unreadable if a device is stolen | Required by several compliance frameworks |
| Patch management | Keeps OS and software updated | Closes known vulnerabilities before attackers exploit them |
| PAM (Privileged Access Management) | Limits who can access sensitive systems | Reduces insider threat and credential abuse |
For regulated sectors, EDR is no longer optional. Unlike traditional antivirus, EDR monitors device behavior continuously, which means it can catch threats that have never been seen before. Signature-only antivirus misses new and modified malware variants, a critical gap in environments handling proprietary aerospace specifications or manufacturing process data.
Pro Tip: Do not choose between antivirus and EDR. Run both. Antivirus handles high-volume known threats efficiently, while EDR provides the behavioral visibility needed to catch sophisticated attacks. Together, they cover far more ground than either does alone.
Reviewing critical controls for small business environments is a practical starting point. From there, working with a provider offering managed endpoint services ensures these controls are configured, monitored, and updated consistently.
Compliance frameworks and endpoint security requirements
Understanding the technical layers is vital, but to stay in business many organizations must also satisfy strict compliance rules tied directly to how endpoints are managed.
If your company is part of a defense or aerospace supply chain, compliance is not a checkbox exercise. It is a condition of doing business. NIST frames endpoint security in SP 800-53 Rev. 5, SP 800-171 covering malicious code protection and monitoring, the Cybersecurity Framework (CSF), and Zero Trust principles. Each framework has specific endpoint requirements.
| Framework | Key endpoint requirements | Who it applies to |
|---|---|---|
| NIST SP 800-171 | Malicious code protection, system monitoring, access control | DoD contractors handling CUI |
| CMMC Level 2 | 110 practices from NIST 800-171, including endpoint controls | Defense supply chain companies |
| NIST CSF | Identify, protect, detect, respond, recover at device level | Broad applicability, widely adopted |
| Zero Trust | Continuous device verification, least-privilege access | Organizations modernizing security posture |
Endpoint security supports CMMC and NIST 800-171 compliance by protecting CUI in supply chains, CAD/CAM systems, and shop-floor devices. Without strong endpoint controls, passing a CMMC assessment is nearly impossible.
Here are the steps small manufacturers and aerospace suppliers should follow to align endpoint security with compliance requirements:
- Inventory every endpoint including shop-floor controllers and mobile devices
- Map each device to the data it accesses and the framework requirements that apply
- Deploy required controls such as EDR, encryption, and patch management
- Document your policies for device access, patching schedules, and incident response
- Test and audit regularly to verify controls are functioning as intended
For businesses navigating endpoint security for compliance requirements, the documentation and audit trail are just as important as the technology itself. Assessors want evidence, not just tools.
Special challenges: BYOD, IoT, and unmanaged endpoints
A solid endpoint security program is not just about mainstream business PCs. It must extend to tricky edge cases often found in today's industrial setups.
Unmanaged BYOD endpoints, embedded IoT in manufacturing, and server endpoints present unique challenges that standard endpoint tools were not always designed to handle. BYOD (bring your own device) means employees use personal phones or laptops to access business systems. IoT refers to internet-connected equipment like sensors, cameras, and programmable logic controllers. Unmanaged endpoints are devices on your network that have no security agent installed.
Common challenges and worst-case scenarios include:
- BYOD devices carrying personal malware onto business networks
- IoT sensors running outdated firmware with no patch path available
- Shop-floor controllers that cannot support traditional endpoint agents
- Unmanaged devices creating blind spots in your monitoring coverage
- Shadow IT where employees connect unauthorized devices without IT awareness
EDR solutions generate significantly more data than traditional antivirus, which can complicate monitoring for small IT teams without dedicated resources. The volume of alerts requires either skilled internal staff or a managed service provider to triage effectively.
Pro Tip: Start with a complete device inventory before deploying any new security tool. You cannot protect what you cannot see. Isolate high-risk devices like legacy IoT systems onto a separate network segment rather than applying blanket policies that may not work on every device type.
For businesses assessing IoT and BYOD device risks, the first priority is visibility. Know exactly what is on your network, then decide how to protect or isolate each category.
Device-level protection versus network security: Why both matter
Managing unconventional and personal devices sheds light on the limits of network-only defenses. Let's contrast endpoint security with classic network security to see why both are necessary.
Network security and endpoint security are often confused, but they operate at different layers and catch different threats. Key differences include:
- Network security monitors traffic between devices and blocks threats at the perimeter or between segments
- Endpoint security monitors what is happening on the device itself, including processes, file changes, and user behavior
- Network tools may miss encrypted malicious traffic or threats that originate inside the network
- Endpoint tools may not see lateral movement between devices without network visibility
- Zero Trust requires verification at both layers continuously, not just at login
Host-based firewalls on each endpoint complement your network firewall by controlling traffic at the device level. Network segmentation limits how far an attacker can move if one device is compromised. Together, they create overlapping layers of defense.
"Relying on network security alone is like locking the front door but leaving every interior room open. Endpoint security ensures that even if an attacker gets inside, each device presents its own barrier."
Endpoint security is distinct from network security at the device level versus traffic monitoring, and integrating both with Zero Trust principles provides continuous verification across your environment. For small manufacturers and aerospace businesses, this layered approach is not excessive. It is the baseline required by most compliance frameworks.
Reviewing network security segmentation practices alongside endpoint controls gives your business the best chance of containing an incident before it becomes a breach.
Our perspective: The compliance clock is already ticking
Many small manufacturers and aerospace suppliers treat endpoint security as something to address after winning a contract. That logic is backward. By the time a CMMC assessment is scheduled, the gaps in your endpoint controls are already a liability. Remediation takes months, not days.
The businesses that stay eligible for defense contracts are not necessarily the largest or most technically sophisticated. They are the ones that built consistent, documented security habits early. Endpoint security is where that discipline starts. Every unpatched device, every unmonitored personal phone on your network, and every shop-floor controller running outdated firmware is a gap that an assessor will find and that an attacker may find first.
The uncomfortable truth is that most breaches targeting small manufacturers do not involve exotic hacking techniques. They exploit basic failures: weak credentials, unpatched software, and endpoints with no behavioral monitoring. Fixing those fundamentals is not glamorous, but it is what actually keeps your business operating and your contracts intact.
Protect your endpoints with Symmetry Network Management
If this article raised questions about your current endpoint security posture, that reaction is worth acting on.

Symmetry Network Management works directly with small manufacturers and aerospace suppliers to assess, deploy, and manage endpoint security controls that meet CMMC, NIST 800-171, and other regulatory requirements. From EDR deployment and patch management to 24/7 monitoring and compliance documentation, the team handles the technical details so you can focus on running your business. With fixed pricing and U.S.-based support, there are no surprises. Schedule a free security assessment today to find out exactly where your endpoints stand and what it takes to close the gaps before they become a problem.
Frequently asked questions
What types of devices are considered endpoints?
Endpoints include desktops, laptops, servers, smartphones, tablets, shop-floor controllers, and IoT systems connected to your business network.
Why is endpoint security important for manufacturing and aerospace?
Endpoint security supports CMMC and NIST 800-171 compliance by protecting CUI in supply chains, CAD/CAM systems, and shop-floor devices, which directly affects supply chain eligibility.
How is endpoint security different from network security?
Endpoint security is distinct from network security because it protects individual devices and their behavior, while network security focuses on monitoring and controlling traffic between devices.
Do businesses need both antivirus and EDR for endpoint security?
Yes. Layered controls using antivirus and EDR together provide broader protection against both known threats and the behavioral anomalies that signature-based tools miss.
