Small businesses in manufacturing, aerospace, and professional services carry a common misconception: that cybercriminals only go after Fortune 500 companies. The reality is far more unsettling. 43% of attacks target small businesses, and manufacturing sits at the top of the hit list. If your operation relies on connected equipment, sensitive contracts, or client data, you are already in the crosshairs. This guide breaks down what cyber insurance actually covers, how it works in practice, why certain industries face unique exposure, and what practical steps you can take to protect what you have built.
Table of Contents
- The real threat landscape: Cyber risks for small businesses
- What cyber insurance covers—and why it's different from other business insurance
- Special considerations for manufacturing, aerospace, and professional services
- How cyber insurance strengthens security—and why uptake is still low
- A realistic perspective: What most guides miss about cyber insurance for small business
- Protect your company with smart cyber risk strategies
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Small business prime targets | 43% of cyber attacks hit small businesses, with manufacturing suffering most from ransomware. |
| Coverage goes beyond basics | Cyber insurance addresses both direct costs and legal liabilities after an attack. |
| Custom coverage needed | Manufacturing and aerospace require endorsements for OT, IP, and supply chain risk. |
| Security boosts eligibility | Strong controls and compliance are usually required for affordable and comprehensive policies. |
| Insurance isn’t enough | True resilience depends on combining sound security practices and risk transfer. |
The real threat landscape: Cyber risks for small businesses
The idea that small businesses fly under the radar of cybercriminals is one of the most dangerous myths in the industry. Attackers know that smaller companies often have weaker defenses, less dedicated IT staff, and more to lose per incident relative to their size. That combination makes small businesses attractive, not invisible.
Manufacturing is the hardest-hit sector by a significant margin. Ransomware incidents in manufacturing account for 26 to 65% of all reported attacks, and the average cost of an industrial breach has reached $5.56 million. Even more alarming, 60% of small and medium-sized businesses fail within six months of a major cyber incident. These are not abstract statistics. They represent shops that closed, contracts that were lost, and reputations that never recovered.
"Ransomware attacks set new records in 2025, with manufacturing absorbing the largest share of incidents and facing some of the steepest recovery costs of any sector."
Aerospace companies face a different but equally serious set of risks. Intellectual property theft, export control violations under ITAR, and third-party supply chain breaches are constant threats. A single compromised vendor can expose your entire operation to regulatory penalties and contract termination. Understanding data's role in manufacturing helps clarify just how much is at stake when that data is stolen or corrupted.
Professional services firms, including legal, financial, and engineering consultancies, hold sensitive client information that is highly valuable on the dark web. These businesses are also frequent entry points for attackers targeting larger clients through trusted relationships.
Top cyber risks by sector:
- Manufacturing: Ransomware locking operational technology (OT), production downtime, IP theft, and supply chain compromise
- Aerospace: ITAR violations from data exfiltration, sabotage of design files, and third-party vendor breaches
- Professional services: Client data theft, business email compromise, and ransomware targeting billing systems
| Sector | Primary threat | Average breach impact |
|---|---|---|
| Manufacturing | Ransomware, OT disruption | $5.56M per incident |
| Aerospace | IP theft, supply chain breach | High regulatory exposure |
| Professional services | Data theft, email fraud | Client liability, reputation loss |
Proper securing of manufacturing networks and implementing network segmentation are foundational steps, but they are not enough on their own. Financial protection through insurance is the layer that keeps a business alive when prevention falls short.

What cyber insurance covers—and why it's different from other business insurance
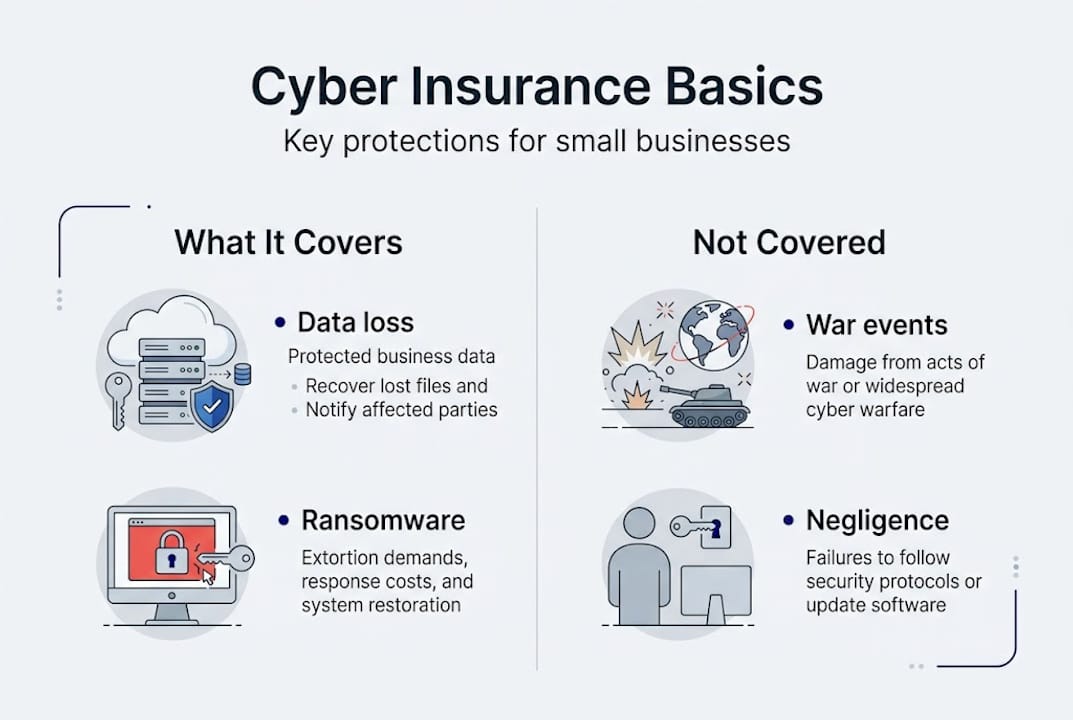
Many business owners assume their general liability or business owner's policy (BOP) covers cyber incidents. It does not. Standard policies were written before the digital age and contain no language addressing data breaches, ransomware, or network outages. Cyber insurance fills that gap with coverage designed specifically for digital risks.
First-party costs are expenses your business incurs directly after an incident. These include incident response and forensic analysis to identify the breach source, lost business income during downtime, ransomware or extortion payments, and the cost of notifying affected customers. Third-party costs cover your legal liability to others, including lawsuits from clients whose data was exposed, regulatory fines, and compliance-related penalties.
According to current market data, cyber insurance pays between 70 and 92% of total incident costs for small and medium-sized enterprises. That coverage ratio can be the difference between recovery and closure.
| Coverage type | Cyber insurance | General liability / BOP |
|---|---|---|
| Data breach response | Yes | No |
| Ransomware payments | Yes | No |
| Business interruption (cyber) | Yes | Rarely |
| Third-party data liability | Yes | Partial |
| Regulatory fines | Yes | No |
How a typical claim works:
- Incident occurs and is reported to the insurer within the required timeframe
- Insurer assigns a breach coach or incident response team
- Forensic investigation identifies scope and cause
- Covered costs are submitted and reimbursed or paid directly
- Post-incident review determines if policy adjustments are needed
For more detail on what controls you need to qualify for coverage, review the cybersecurity controls that most insurers require. Businesses in defense contracting should also review CMMC compliance requirements, as these often align directly with insurance eligibility.
Pro Tip: Before purchasing a policy, read the security requirements carefully. Many claims are denied not because the attack was excluded, but because the business failed to maintain the controls it agreed to at underwriting. See cyber liability insurance details for a breakdown of what insurers typically require.
Special considerations for manufacturing, aerospace, and professional services
Not all cyber insurance policies are created equal, and standard coverage often falls short for businesses in regulated or operationally complex industries. If you work in manufacturing, aerospace, or a compliance-heavy professional services field, you need to look beyond the base policy.
Aerospace and manufacturing companies require specialized endorsements covering intellectual property theft, damage to operational technology, supply chain disruption, and CMMC compliance obligations. These endorsements increase premiums, but they also ensure that the coverage actually applies when something goes wrong.
"A manufacturer that loses production for three days due to ransomware faces not just repair costs, but missed delivery penalties, customer churn, and potential contract termination. Standard policies rarely account for all of these."
Underwriters in these sectors look for specific security practices before offering coverage. Multi-factor authentication (MFA), documented incident response plans, and network segmentation are common requirements. Businesses that cannot demonstrate these controls may be denied coverage or face significantly higher premiums.
Exclusions are another area where businesses get caught off guard. Most policies exclude:
- Acts of war or nation-state attacks (a growing gray area as geopolitical cyber activity increases)
- Incidents caused by failure to apply known patches or updates
- Losses from systems that were not disclosed during underwriting
- Systemic events affecting multiple policyholders simultaneously
Must-check items for SMEs in manufacturing, aerospace, and professional services:
- Confirm OT and industrial control systems are explicitly covered
- Verify supply chain breach scenarios are included
- Check for IP theft endorsements if you hold proprietary designs or formulas
- Ensure CMMC or ITAR compliance support is part of the policy or available as an add-on
- Review sub-limits on ransomware payments, which are often capped below total policy limits
Pro Tip: Ask your broker specifically about endorsements for ITAR and AS9100 solutions if you are in aerospace. A generic policy written for a retail business will not address the regulatory exposure you face.
How cyber insurance strengthens security—and why uptake is still low
Here is a fact that surprises many business owners: carrying cyber insurance often makes your business more secure, not just more protected financially. Insurers require applicants to meet baseline security standards before issuing a policy. That process forces businesses to address gaps they might otherwise ignore.
Despite this benefit, SME cyber insurance penetration sits at roughly 10%. Nine out of ten small businesses are operating without this protection, even as attack volumes continue to climb.
Why businesses skip cyber insurance:
- "We're too small to be a target" (incorrect, as the data shows)
- Perceived cost is too high relative to perceived risk
- Assumption that existing IT or general liability coverage is sufficient
- Complexity of the application process feels overwhelming
- Lack of awareness that cyber-specific policies exist
The financial case for prevention is strong. Research suggests a 7 to 8x return on investment for proactive cybersecurity measures, meaning every dollar spent on controls reduces expected losses by seven to eight dollars. Insurance amplifies that math by covering the residual risk that controls cannot eliminate.
Security steps commonly required by insurers:
| Control | Why insurers require it |
|---|---|
| Multi-factor authentication | Reduces credential-based breaches significantly |
| Endpoint detection and response | Catches threats before they spread |
| Regular data backups | Limits ransomware leverage |
| Employee security training | Addresses the human error factor |
| Patch management program | Closes known vulnerabilities promptly |
Reviewing your crucial security controls before applying for coverage can meaningfully lower your premium. And testing your backups regularly is one of the most effective ways to demonstrate resilience to underwriters while actually building it.
Neither insurance nor controls alone are sufficient. The businesses that recover fastest from incidents are those that treat security as an ongoing practice and use insurance as the financial backstop for the risks that remain.
A realistic perspective: What most guides miss about cyber insurance for small business
Most articles on cyber insurance treat it as a checkbox. Buy the policy, file it away, move on. That framing misses the point almost entirely.
The uncomfortable truth is that most cyber insurance claims are triggered by non-malicious, everyday human errors: an employee clicking a phishing link, a misconfigured cloud storage bucket left open, or a forgotten system that never received a critical update. The threat is not always a sophisticated attacker. It is often a distracted team member on a busy Tuesday.
Policies also are not fire-and-forget instruments. If your business fails to maintain the security controls you agreed to at underwriting, your insurer can deny your claim. That is a painful lesson to learn after an incident has already cost you weeks of downtime.
The real value of cyber insurance is what it forces you to do before you ever file a claim. The application process surfaces gaps. The requirements push you toward better practices. The coverage gives you the confidence to operate without fear of a single incident wiping out years of work.
For holistic network security, the combination of strong controls and appropriate coverage is what genuinely builds resilience. One without the other is a partial answer to a complete problem.
Pro Tip: Invest in building a security culture across your team, not just in purchasing policy paperwork. Training, awareness, and clear incident reporting procedures reduce the frequency of claims and keep your coverage valid when you need it most.
Protect your company with smart cyber risk strategies
Understanding your exposure is the first step. Taking action is what actually protects your business. Symmetry Network Management works with small businesses in manufacturing, aerospace, and professional services to close security gaps, meet compliance requirements, and prepare for the unexpected.

Our team can help you assess your current security posture, identify what coverage you likely need, and implement the controls that insurers require. Whether you are exploring managed IT services for the first time or looking to strengthen an existing program, we offer a free assessment to get you started. Review our critical security controls guide and explore how business continuity backup planning fits into your overall risk strategy. Reach out today to take the guesswork out of cyber risk.
Frequently asked questions
How much does cyber insurance cost for manufacturing or aerospace small businesses?
Premiums are typically higher in these sectors due to the severity of operational risks, the need for OT endorsements, and supply chain exposure. Exact costs vary based on revenue, security controls in place, and coverage limits selected.
Does cyber insurance cover all types of cyber attacks?
Most policies cover a broad range of incidents, but war exclusions and denials for failure to maintain required controls are common. Always read the exclusions section before purchasing.
Is cyber insurance required for CMMC or by certain clients?
It is not legally mandated, but CMMC compliance aligns closely with insurance eligibility requirements, and many defense contracts now stipulate coverage as a condition of doing business.
Why do most small businesses skip cyber insurance even with high risks?
The ~10% SME penetration rate reflects a mix of cost concerns, misplaced confidence in existing policies, and the mistaken belief that small businesses are not attractive targets.
Does having insurance mean my business is fully protected?
No. Insurance mitigates financial loss but cannot replace strong cybersecurity controls, trained employees, and a proactive risk management culture. Coverage and prevention must work together.
Recommended
- Symmetry Network Management | Managed IT Services
- 5 Critical Security Controls Every Small Business Needs | Symmetry Network Management
- Top 10 IT Infrastructure Mistakes Small Businesses Make - Symmetry Network Management
- Securing Microsoft 365 for Small Business | Symmetry Network Management
- Why Invest in Cybersecurity: Protecting Houston Businesses
