Ransomware hits your manufacturing floor at 6 a.m. on a Monday. Machines stop. Orders back up. Your team scrambles. Within hours, you're facing production losses, customer complaints, and a growing question: are you legally required to report this, and to whom? For small businesses in manufacturing, aerospace, and professional services, a cyber incident is never just an IT problem. It triggers a cascade of operational, financial, and regulatory consequences that can be hard to reverse if you're not prepared. This guide walks you through every phase of an effective cyber response, from initial containment to post-incident review, so you can act with confidence when it counts.
Table of Contents
- Understand the threat landscape and requirements
- Preparation: build your cyber incident response toolkit
- Execution: step-by-step response when a cyber threat hits
- Verification: post-incident review and continuous improvement
- Most guides overlook: safety-first for manufacturing or aerospace recovery
- Next steps: connect with trusted experts for ongoing protection
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Regulatory reporting matters | Know your federal and state notification deadlines to avoid penalties and build trust. |
| Incident response must be tested | Regular drills and plan reviews ensure you avoid costly missteps during a cyber attack. |
| Prioritize safety in manufacturing | Operational safety is crucial when recovering from incidents in manufacturing or aerospace environments. |
| Continuous improvement loop | Post-incident review and plan updates keep your defenses sharp and responsive. |
Understand the threat landscape and requirements
Before you can respond effectively, you need to know what you're up against. Small businesses are not low-priority targets. In fact, they're frequently selected precisely because attackers assume their defenses are weaker than those of large enterprises.
The most common threats hitting your sector:
- Ransomware: Encrypts files and demands payment. Especially damaging in manufacturing and aerospace where operational downtime means immediate financial loss.
- Phishing: Deceptive emails that steal credentials or install malware. Professional services firms are frequently targeted because employees handle sensitive client data.
- Business email compromise (BEC): Attackers impersonate executives or vendors to redirect payments. This is a growing threat for small firms with limited financial controls.
- Supply chain attacks: Malicious code inserted through a trusted vendor's software. Aerospace contractors face heightened risk given their interconnected supplier networks.
- Insider threats: Intentional or accidental misuse of access by employees or contractors.
Understanding where you're most exposed is the starting point for building real defenses. For practical guidance on strengthening your baseline, review these cybersecurity steps aligned to common small business risks.
Regulatory reporting: know your deadlines before an incident
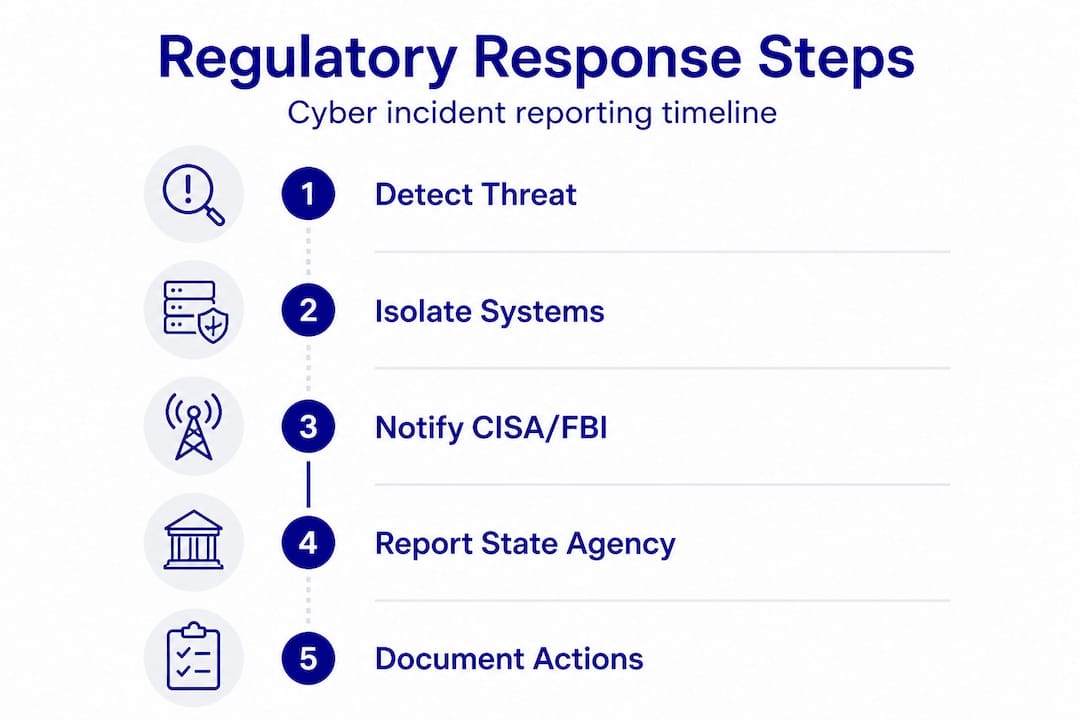
One of the most overlooked aspects of cyber response is the regulatory clock. Many small business owners assume reporting is optional or only applies to large enterprises. It isn't.
| Regulatory body / law | Who it applies to | Reporting deadline |
|---|---|---|
| CISA and FBI | All U.S. businesses | Immediately upon discovery |
| State breach notification laws | Businesses holding personal data | Typically 30 to 90 days |
| DoD/DFARS (CUI handlers) | Defense contractors | 72 hours |
| HIPAA (if applicable) | Healthcare-adjacent businesses | 60 days |
The FTC's cybersecurity guidance reinforces that reporting to CISA and the FBI should happen immediately, state breach laws typically require notification within 30 to 90 days, and DoD contractors must report within 72 hours when controlled unclassified information (CUI) is involved. Missing these windows can mean fines on top of the breach itself.
For log management, CISA recommends that small businesses centralize system logs, configure real-time alerts, and designate a crisis response team before an incident ever occurs. These aren't advanced practices. They're foundational steps that most small businesses haven't taken yet.
Preparation: build your cyber incident response toolkit
With requirements and threats in mind, assembling a response toolkit ensures you're ready for fast action. Preparation is the single biggest variable between a breach that costs you a few days and one that costs you the business.
Your response toolkit should include:
- Centralized logging platform: Captures activity across endpoints, servers, and network devices. Without logs, you can't trace what happened or prove compliance.
- Alert and monitoring system: Flags anomalies in real time, such as unusual login times, large data transfers, or disabled security tools.
- Offline and cloud backups: Protects against ransomware by ensuring data can be restored without paying a ransom. More on this in the execution section.
- Documented incident response plan (IRP): A written playbook that tells your team exactly what to do, who to call, and how to communicate internally and externally.
- Crisis response team: Designated individuals with defined roles, including a technical lead, a communications point of contact, and a compliance officer or legal contact.
Proactive vs. reactive: a direct comparison
| Approach | Average response time | Regulatory risk | Recovery cost |
|---|---|---|---|
| Proactive (IRP, monitoring, backups) | Hours to 1 day | Low to moderate | Contained |
| Reactive (no plan, manual detection) | Days to weeks | High | Potentially severe |
The contrast is stark. Businesses that invest in preparation consistently recover faster and face fewer regulatory penalties. According to NIST guidance for manufacturers, professional services and manufacturing firms should align their preparation with the NIST Cybersecurity Framework (CSF), and specifically develop incident response, disaster recovery, and business continuity plans as distinct but connected documents.
CISA also emphasizes that designating a crisis response team is not optional for businesses that want to meet federal standards. Your team doesn't need to be large. Even a three-person group with defined responsibilities is far more effective than an ad hoc response under pressure.
Pro Tip: If your small manufacturer or aerospace firm handles government contracts, review this small manufacturer guide to understand the specific CMMC and NIST 800-171 requirements that shape your IRP obligations. And for a solid technical foundation, the IT security essentials article outlines the baseline controls every shop floor environment needs.
Execution: step-by-step response when a cyber threat hits
With preparation handled, here's exactly what to do during an incident. Speed and discipline matter. Every minute of uncontrolled spread means more recovery time and higher exposure.
Immediate response steps:
- Isolate affected systems. Disconnect compromised machines from the network immediately. This stops lateral movement. Do not shut them down entirely as this can destroy volatile forensic evidence.
- Activate your incident response plan. Pull up your documented IRP and follow it. Assign roles. Brief your crisis team. Don't improvise.
- Assess the scope. Determine which systems, data, and users are affected. This informs both your recovery priority and your reporting obligations.
- Preserve evidence. Take screenshots, save logs, and document the timeline of events. Regulators and cyber insurers will ask for this.
- Notify internal stakeholders. Alert leadership, legal, and HR as appropriate. Internal communication should be coordinated and factual.
- Report to authorities. Based on your incident type, notify CISA, the FBI, and any relevant state agencies. If you handle DoD contracts and CUI is involved, your window is 72 hours.
- Begin recovery. Restore systems from verified clean backups. Validate that systems are clean before reconnecting them to the network.
- Communicate externally. Notify affected clients, partners, or customers as required by law and contract. Be transparent and precise.
"An untested incident response plan is not a plan. It's a document."
The FTC's guidance is direct: test your IRP regularly using tabletop exercises and real drills. Plans that haven't been practiced will fail under the pressure of a live incident. Offline backups following the 3-2-1 rule (three copies, two media types, one offline or offsite) are a specific FTC recommendation for small businesses facing ransomware exposure.
Special considerations for manufacturing and aerospace:
NIST guidance for manufacturers draws a critical distinction between IT systems and operational technology (OT) or industrial control systems (ICS). On a factory floor or in an aerospace facility, these systems run physical processes. A recovery sequence that works fine for a corporate IT environment can cause equipment damage or physical safety risks if applied to OT environments without modification.
Keep IT and OT recovery tracks separate. Use NIST's Cyber Security Evaluation Tool (CSET) to assess your OT environment independently. Physical safety comes before data restoration, always.
You can learn more from real-world data breach lessons that apply directly to small business scenarios, and review a dedicated network security guide built around manufacturing environments.
Verification: post-incident review and continuous improvement
After the incident, take these steps to ensure you're not exposed next time. Recovery doesn't end when the systems come back online. The real work of prevention starts here.
Post-incident review checklist:
- Document what happened: Write a clear timeline from initial detection to full recovery. Include what worked, what didn't, and where delays occurred.
- Identify root cause: Was it a phishing email? An unpatched system? A misconfigured firewall? The root cause determines the fix.
- Audit your controls: Test whether your security tools detected the threat promptly. If they didn't, find out why.
- Test backup restoration: Verify that your backups actually work. A backup you've never tested is a backup you can't trust.
- Update your IRP: Revise your plan based on what you learned. If a notification step was missed or a contact was unreachable, fix it now.
- Brief your team: Share key lessons across your organization. Cyber awareness is a collective responsibility, not just an IT function.
NIST SP 800-61r3 establishes that post-incident reviews are a formal part of a mature incident response capability. The guidance specifically emphasizes prioritizing high-impact assets during recovery and using each incident as a structured input into a continuous improvement loop. This isn't a one-time exercise. It's an ongoing discipline.
Pro Tip: Backup testing is one of the most commonly skipped steps in small business continuity planning. Review this backup testing resource to understand how to validate restoration capability before you need it in a crisis. Additionally, if you've been wondering whether your cyber response planning affects your insurance premiums and coverage, this article on cyber insurance insights is worth reading before your next renewal.
The continuous improvement loop isn't complicated. Every incident, even a near-miss, generates data you can use to make your next response faster and more effective. Businesses that treat post-incident reviews as optional often find themselves responding to the same type of attack more than once.
Most guides overlook: safety-first for manufacturing or aerospace recovery
Most cyber incident response guides are written with corporate IT environments in mind. They focus on data confidentiality, notification timelines, and system restoration. That framework is sound for a law firm or a consulting agency. But it breaks down quickly on a factory floor or inside an aerospace facility.
The missing piece is operational safety. In manufacturing and aerospace environments, IT systems and OT/ICS systems are often more interconnected than operators realize. A firewall protecting a corporate network might share infrastructure with a system managing machine speed, pressure, or temperature. When attackers compromise one layer, the risk doesn't stay confined to data. It can extend to physical processes and, in worst-case scenarios, to worker safety.
Conventional IT-first response protocols can actually create new hazards in these environments. Forcing an immediate shutdown of all connected systems without understanding which ones control physical processes can cause equipment faults, production damage, or hazardous conditions. NIST's guidance for manufacturers explicitly addresses this by recommending that IT and OT recovery be kept on separate tracks, with physical safety evaluated before any reconnection to the network.
What this means practically: your incident response plan needs two parallel tracks. One for your business IT systems (email, ERP, file shares, workstations) and one for your production floor systems. The people making recovery decisions for each track may not be the same people. Your IT lead might not understand the operational implications of bringing a programmable logic controller (PLC) back online in a certain sequence. Your operations manager might not understand network segmentation. Both need to be at the table.
This manufacturing cybersecurity guide covers the structural differences that make manufacturing environments uniquely complex in a cyber incident. The bottom line: if your business involves physical production or critical aerospace systems, your IRP needs to be built with your operations team, not just your IT provider.
Next steps: connect with trusted experts for ongoing protection
Building a solid cyber incident response framework is a significant step forward. Maintaining it over time, while running a business, is where most small organizations struggle.

Symmetry Network Management works specifically with small businesses in manufacturing, aerospace, and professional services to put these frameworks in place and keep them current. From managed IT and security services that include 24/7 monitoring and endpoint protection to dedicated backup and continuity solutions that ensure your 3-2-1 strategy is actually working, the team brings industry-specific expertise without the cost of an internal IT department. Symmetry also provides guidance on network segmentation practices that protect OT environments from IT-side threats. If you're not sure where your current gaps are, a free assessment is the right starting point. You'll get a clear picture of your security posture and a practical roadmap for what to address first.
Frequently asked questions
What is the first thing a small business should do after a cyber attack?
Immediately activate your incident response plan, isolate affected systems, and notify the appropriate authorities. Per FTC guidance, reports to CISA and the FBI should go out right away, with state and DoD timelines following based on the data involved.
How often should incident response plans be tested?
Test your IRP at least once per year and after any major process or personnel change. The FTC recommends combining tabletop exercises with real-world drills to catch gaps before a live incident exposes them.
What are key regulatory reporting deadlines for cyber incidents?
Reporting deadlines vary by obligation: CISA and the FBI should be notified immediately, most state breach notification laws require action within 30 to 90 days, and DoD contractors handling CUI must report within 72 hours of discovery.
What is the 3-2-1 backup rule?
The 3-2-1 rule means keeping three copies of your data on two different types of storage media, with one copy stored offline or offsite. This backup strategy protects against ransomware by ensuring at least one clean copy is always out of reach of an attacker.
How does professional services compliance differ from manufacturing?
Professional services firms primarily align to NIST CSF with an emphasis on strong log management and data protection policies. Manufacturing and aerospace firms face additional complexity because they must also separate IT from OT/ICS, assess industrial control systems using tools like CSET, and build safety-first recovery procedures into their incident response plans.
